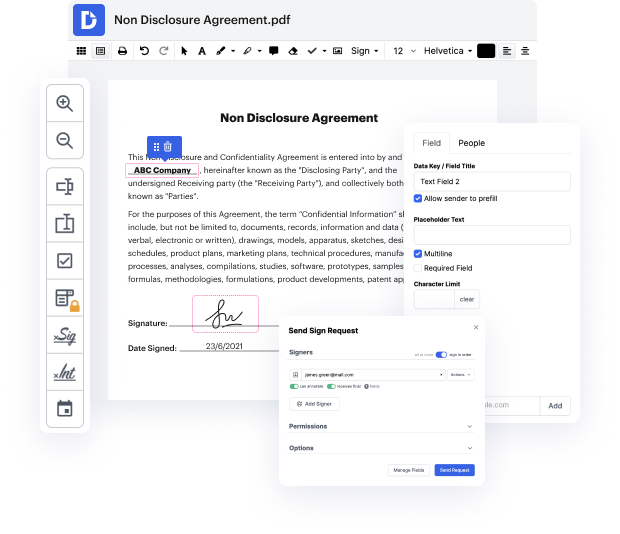
At the first blush, it may seem that online editors are pretty much the same, but you’ll realize that it’s not that way at all. Having a powerful document management solution like DocHub, you can do much more than with standard tools. What makes our editor exclusive is its ability not only to rapidly Inject code in Living Will but also to create documentation completely from scratch, just the way you need it!
Despite its comprehensive editing capabilities, DocHub has a very easy-to-use interface that offers all the features you need at your fingertips. Therefore, altering a Living Will or a completely new document will take only a couple of moments.
Register for a free trial and celebrate your greatest-ever document-related practice with DocHub!
A code injection attack is when the attacker puts their own code into an existing data stream. This is often enabled because of bad programming with an application. An application shouldnt allow you to put your own code into a data stream. But, often, the code is not checked by the application, and attackers are able to exploit that vulnerability. Theres many different types of code that you can inject. You can inject HTML, or LDAP, or SQL code-- and any one of those may be able to manipulate or gather information from a machine, especially if you have control over the type of code that you would put into that data stream. One very common code injection type is a SQL injection. SQL stands for Structured Query Language-- or SQL. This is a very common relational database used on many websites. If you can circumvent the web front end, then you can gain access to the data thats in that database. Of course, the web front end should not allow these types of requests, but if the input is n
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



