Safety should be the main consideration when searching for a document editor on the web. There’s no need to waste time browsing for a trustworthy yet cost-effective service with enough functionality to Inject code in Conference Itinerary. DocHub is just the one you need!
Our solution takes user privacy and data protection into account. It complies with industry regulations, like GDPR, CCPA, and PCI DSS, and continuously improves its compliance to become even more hazard-free for your sensitive data. DocHub enables you to set up two-factor authentication for your account configurations (via email, Authenticator App, or Backup codes).
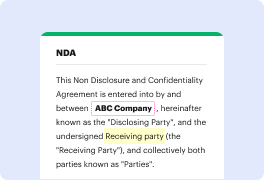
For that reason, you can manage any documentation, including the Conference Itinerary, risk-free and without hassles.
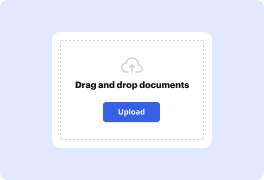
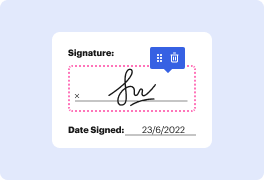
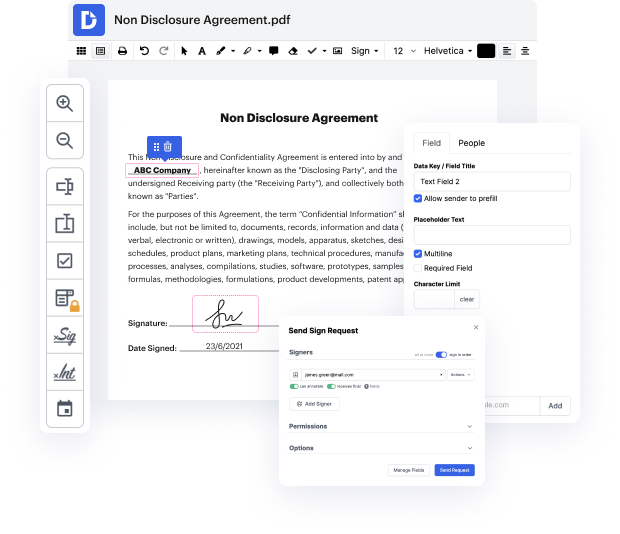
Apart from being trustworthy, our editor is also very straightforward to use. Adhere to the guideline below and make sure that managing Conference Itinerary with our service will take only a few clicks.
If you frequently manage your paperwork in Google Docs or need to sign attachments received in Gmail rapidly, DocHub is also a good choice, as it perfectly integrates with Google services. Make a one-click file import to our editor and complete tasks within minutes instead of continuously downloading and re-uploading your document for processing. Try out DocHub today!
Hey everybody. Eh, welcome to Please Inject-Me, a x64 Code Injection. So lets start. Eh, a little about me. Eh, my name is Alon. Ive been to cybersecurity industry for about 7 years. Ehm, started at the IDF in the Intelligent Division, and now working at Deep Instinct. Ehm, at Deep Instinct Im, eh, researching for new attack vectors, doing some heuristics, ehm, and ehm, finding, eh, new ways to attack. Ehm also reversing malwares, eh, so thats pretty much about me. Okay, so any stock, eh, first Im going to give you a short introduction about code injections, so its going to be really short. Im going to talk about what is Inject-Me, eh, the new code inject- injection technique I found. Ehm, then Im going to give you a little bit, eh, of technical back -background just to know eh things that you need to know before you can abuse the method, eh, to do the code injection. And at the end theres going to be, ehm, a little flow of how to do the code injection. Okay, so what is c
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



