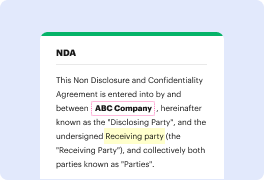
If you edit files in various formats day-to-day, the universality of the document solution matters a lot. If your tools work for only a few of the popular formats, you may find yourself switching between software windows to inject code in pdf and manage other document formats. If you want to take away the hassle of document editing, go for a solution that can easily handle any extension.
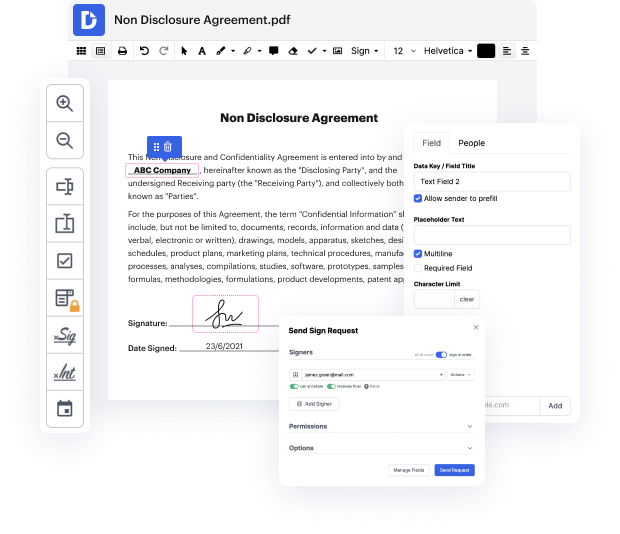
With DocHub, you do not need to focus on anything short of the actual document editing. You won’t have to juggle applications to work with various formats. It can help you modify your pdf as easily as any other extension. Create pdf documents, modify, and share them in a single online editing solution that saves you time and improves your productivity. All you have to do is sign up a free account at DocHub, which takes just a few minutes.
You won’t need to become an editing multitasker with DocHub. Its feature set is sufficient for fast document editing, regardless of the format you need to revise. Start by registering a free account and see how straightforward document management may be with a tool designed specifically for your needs.
application security is something that we all need to take seriously especially when you create small services that might allow you to do your job faster or small simple things like hey converting even markdown code into HTML or to a PDF file so in this video I want to showcase a challenge from the Seesaw Capture the Flag competition qualifiers that was just simply that converting markdown into a PDF and how we might be able to explore some vulnerabilities and ultimately compromise it lets dive in before we dive into the video heres a quick note from todays sponsor there are so many vulnerabilities out there like prototype pollution SQL injection remote code execution and more theyre fun to play with in CTF challenges pen testing and ethical hacking but theyre not so fun when theyre in your own applications and that is where sneak comes in sneak automatically scans your code dependencies containers and config files finding and fixing vulnerabilities in real time heres how easy
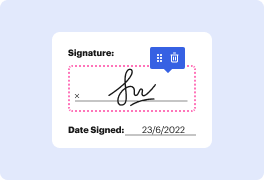
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



