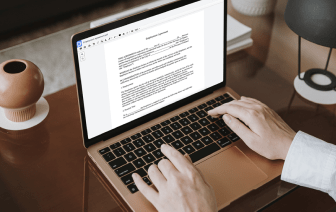
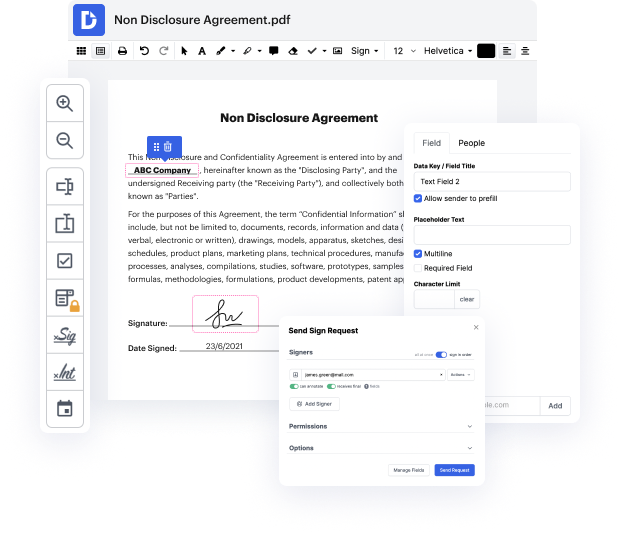
DocHub makes it quick and straightforward to inject clause in DBK. No need to instal any software – simply add your DBK to your profile, use the simple drag-and-drop editor, and quickly make edits. You can even work on your desktop or mobile device to modify your document online from anywhere. That's not all; DocHub is more than just an editor. It's an all-in-one document management platform with form creating, eSignature features, and the option to let others fill in and eSign documents.
Every file you edit you can find in your Documents folder. Create folders and organize records for easier search and retrieval. Additionally, DocHub ensures the safety of all its users' data by complying with stringent security protocols.
hello guys and welcome to c cube digital youtube channel and today we will be solving the sql injection lab from port zigga so in this video we will be solving the very first lab of sql injection from port zigga academy that is retrieving hidden data and we will be solving the upcoming challenges in the upcoming videos so here it is written that receiving hidden data and in some websites you will find a get parameter like this like category is equal to gifs and something like this you are a little be there and then you can just try to put in a semicolon at the end of this uh parameter and check if thereamp;#39;s any error popping out so if you are getting an error in this uh after putting the single quote in the end then you will be certain that the the query is being processed and this site is vulnerable to sql injection attacks so itamp;#39;s not always a single quotation itamp;#39;s some time or double quotes or sometimes even a curly braces that is a round basis uh so uh next uh