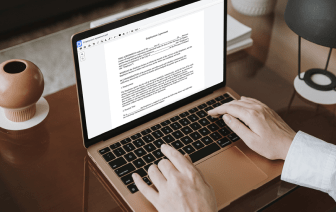
It is usually difficult to get a solution that may deal with all your corporate needs or provides you with appropriate instruments to manage document creation and approval. Opting for a software or platform that includes crucial document creation instruments that simplify any task you have in mind is essential. Although the most in-demand file format to use is PDF, you require a comprehensive software to manage any available file format, such as raw.
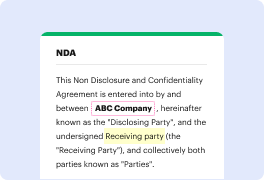
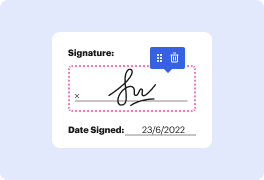
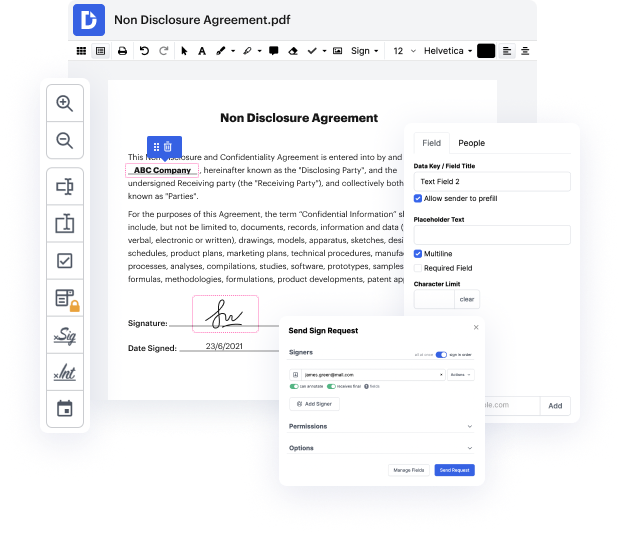
DocHub helps to ensure that all your document creation demands are covered. Modify, eSign, rotate and merge your pages based on your preferences by a mouse click. Deal with all formats, such as raw, effectively and . Regardless of the file format you start working with, it is possible to change it into a required file format. Preserve a great deal of time requesting or looking for the appropriate file type.
With DocHub, you don’t require extra time to get familiar with our interface and editing procedure. DocHub is surely an intuitive and user-friendly software for anybody, even all those with no tech education. Onboard your team and departments and transform file managing for the firm forever. include password in raw, generate fillable forms, eSign your documents, and have processes finished with DocHub.
Make use of DocHub’s comprehensive function list and rapidly work with any file in any file format, which includes raw. Save time cobbling together third-party solutions and stick to an all-in-one software to improve your daily procedures. Start your free DocHub trial today.
hello and this is sunny welcome back today my topic is salt and pepper to understand these two concepts a little background knowledge about hash algorithm is helpful hash algorithm is commonly used to fool passwords for example when I log into Twitter I type in sunny south as my username and my password abc123 when I click Submit my password would be hashed to a digest or hashed hash algorithm is not reversible giving a hash value I could not get his original input keep in mind all passwords in any secure database should be stored in the form of a digest or hash every time you log in your password is a hashed to a digest which is then compared against the one stored in the database thats why we say hash algorithm is mainly used for comparison purpose not for encryption however hackers can cracked hashed passwords with a dictionary attack or brutal force attack or rainbow table attacks in order to make is more difficult for hackers to crack our passwords salt and pepper are used [Musi