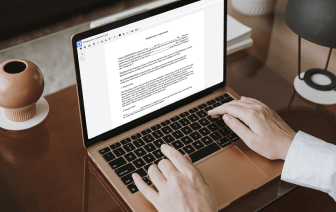
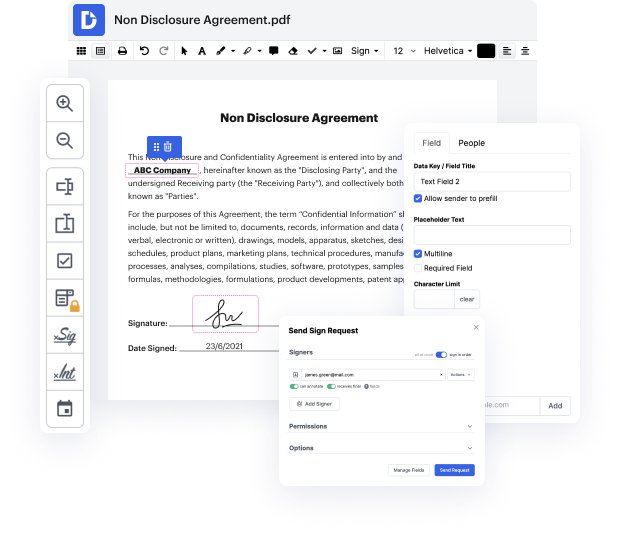
Time is an important resource that every enterprise treasures and tries to convert in a advantage. In choosing document management application, be aware of a clutterless and user-friendly interface that empowers consumers. DocHub delivers cutting-edge instruments to enhance your file management and transforms your PDF editing into a matter of a single click. Hide Field Validation in the Proxy Card with DocHub in order to save a ton of time and boost your productivity.
Make PDF editing an easy and intuitive operation that saves you plenty of precious time. Effortlessly adjust your documents and send out them for signing without the need of switching to third-party software. Focus on relevant duties and boost your file management with DocHub right now.
if youre using hacking tools like kali linux and youre not doing anything to hide yourself its kind of dangerous like you could get into trouble you need to learn learn learn hacking [Music] proxies and proxy chains thats how you hide yourself in this video im going to show you how they work and how to set them up in cali linux i also have a crazy challenge at the end a hacking challenge using the knowledge youre going to learn in this video if youre up for it the first five people to complete this challenge will win a six-month membership to this is it and a bag of network chuck coffee and also a huge shout out to it pro tv theyre sponsoring this part of my journey i use them to learn about proxy chains and everything else hacking ive learned so far so if you want to check them out if you want to learn hacking ccna a plus whatever link below use code network chuck 25 off forever so youre ready youre ready to hack you fire up kali linux youve got your tools ready youre rea