COVID forever transformed how organizations see their internal protocols and processes. It affected businesses of all sizes and sectors, posing new challenges for staying connected. The pandemic indicated that all organizations must integrate digital instruments into every day routines. They became important for far more than hybrid working models.
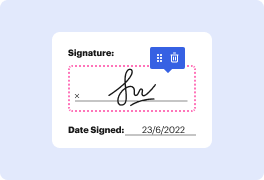
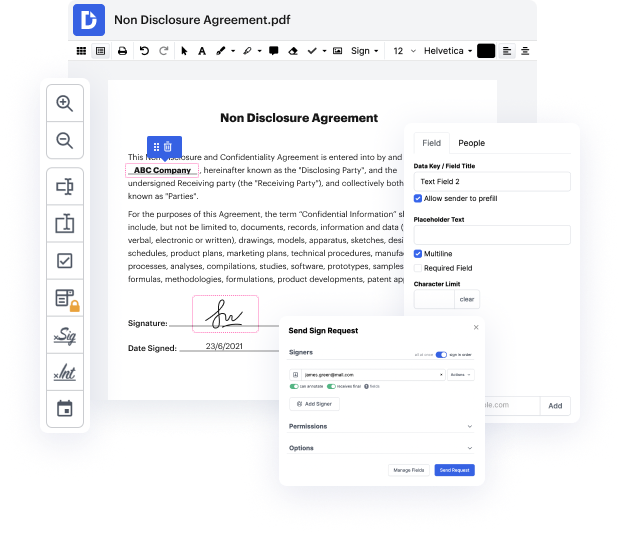
Apps like DocHub enable you to boost your document management and approval operations. DocHub is the go-to instrument for end-to-end online editing and signatures. It helps reduce your everyday contract and agreement generation and approval tasks. Obtain access to Form Application - Digital Certificate innovative editing tools that cover all of your managing needs. Work with any document type and format, create fillable fields, and successfully gather signatures from your teammates and clients. No past training or experience is needed.
With Form Application - Digital Certificate, it is possible to increase the quality of your files, accelerate the approval process, and securely store finished files. Obtain a cost-free DocHub profile right now and change your subscription when you want.
Digital signatures rely on symmetric key cryptography. Before discussing digital signatures, let's understand how symmetric key cryptography works. In asymmetric key cryptography, there are pairs of mathematically related keys. If a message is encrypted with one key, only the other key can decrypt it. Albert and Sheila are discussing how Sheila can send Albert a secret message using asymmetric key cryptography. Sheila generates a pair of keys and sends one key to Albert while keeping the other key. Alternatively, she can put a key in a public place for Albert to access. Albert uses the public key to encrypt the message, which only Sheila can decrypt with the matching private key.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



