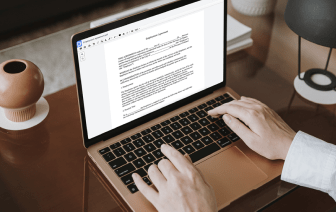
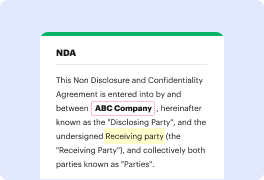
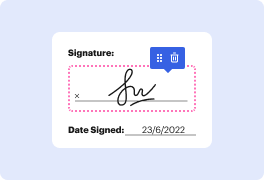
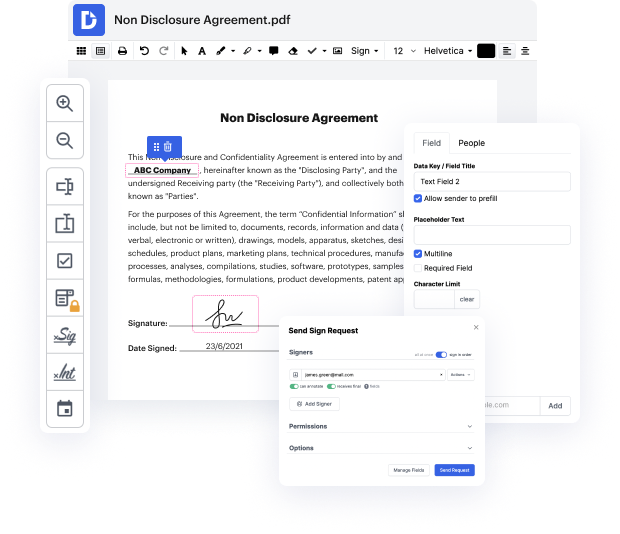
You no longer have to worry about how to fill in identification in ACL. Our extensive solution provides easy and quick document management, enabling you to work on ACL documents in a couple of minutes instead of hours or days. Our platform contains all the tools you need: merging, adding fillable fields, approving forms legally, adding signs, and much more. There’s no need to install extra software or bother with high-priced applications requiring a powerful device. With only two clicks in your browser, you can access everything you need.
Start now and handle all various types of forms professionally!
welcome to the IIs Institute sounds of safety podcast where our community will be delving into a series of critical issues supporting the public sector mission space on todayamp;#39;s episode we return to the IIs cyber security working group for their next installment of the navigating cyber security series weamp;#39;re excited to welcome back Larry Zoro chair of the working group and valued working group member Jeremy Cooper levit as they EXP exp the second core function of the nist CSF framework identify the identify core function is the foundational step designed to help organizations develop an understanding of their cyber security riskmanagement processes assets data capabilities and risk appetite letamp;#39;s hear from Larry and Jeremy as they lay down the groundwork for Effective cyber security risk management hi everybody and welcome to another episode of sounds of safety podcast an IIs podcast and specifically todayamp;#39;s episode is around cyber security and we