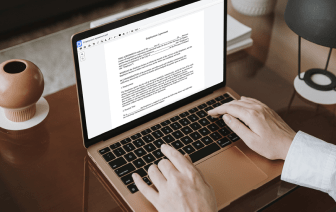
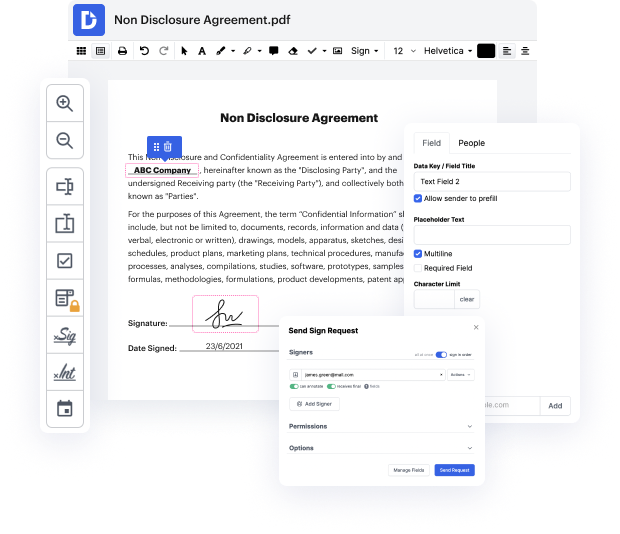
With DocHub, you can easily faint authentication in MCW from anywhere. Enjoy features like drag and drop fields, editable text, images, and comments. You can collect eSignatures safely, include an extra level of protection with an Encrypted Folder, and work together with teammates in real-time through your DocHub account. Make adjustments to your MCW files online without downloading, scanning, printing or sending anything.
You can find your edited record in the Documents folder of your account. Prepare, share, print out, or convert your document into a reusable template. Considering the variety of powerful tools, it’s simple to enjoy seamless document editing and managing with DocHub.
foreign what does the term confidentiality in the context of security refer to option A protecting information from an authorized access option b ensuring systems and data are accessible at all times option C permitting authorized access to information while protecting it from improper disclosure option D ensuring the completeness accuracy and internal consistency of information the correct answer is option C permitting authorized access to information while protecting it from improper disclosure explanation part of the CIA trade confidentiality allows to keep the information visible to only the authorized individual this could be nay information such as credit card details or other personally identified information question two what is the purpose of the CIA Triad in security option A to make security more understandable to management and users option b to define the purpose of security using irrelevant and meaningless words option C to describe Security in a way that only exp