Working with paperwork can be a challenge. Each format comes with its peculiarities, which often leads to complex workarounds or reliance on unknown software downloads to bypass them. The good news is, there’s a tool that will make this process more enjoyable and less risky.
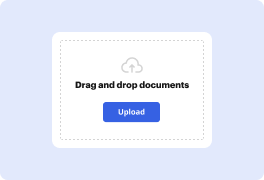
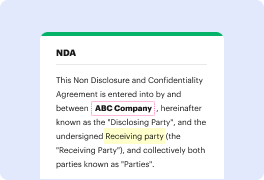
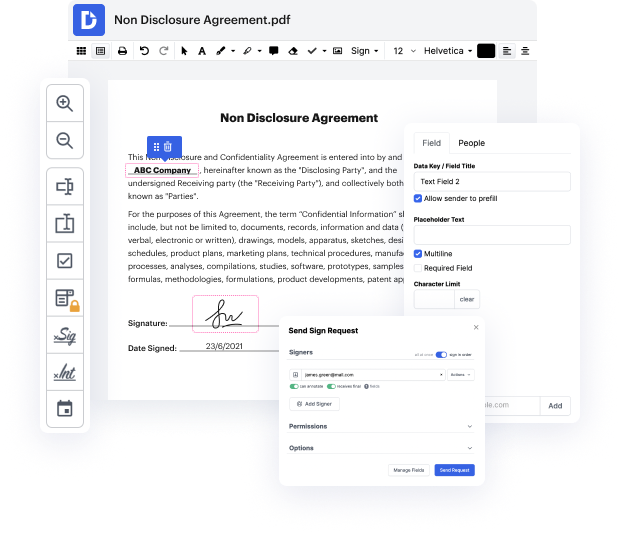
DocHub is a super straightforward yet full-featured document editing solution. It has different tools that help you shave minutes off the editing process, and the ability to Exploit Statement Of Work For Free is only a fraction of DocHub’s capabilities.
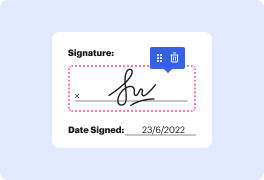
No matter if if you need occasional editing or to edit a multi-page form, our solution can help you Exploit Statement Of Work For Free and make any other desired improvements easily. Editing, annotating, signing and commenting and collaborating on files is simple with DocHub. We support various file formats - select the one that will make your editing even more frictionless. Try our editor free of charge today!
Simon, a vulnerability researcher for Sona Source, discusses a common bypass pattern used to exploit modern web apps. He focuses on finding and disclosing vulnerabilities in open source software like WordPress, Magento 2, MyBB, Zimbra, and the Linux Kernel. Simon's goal is to detail bug chains found in popular web applications that have been hardened, starting with a WordPress one-click remote code execution via CSRF.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



