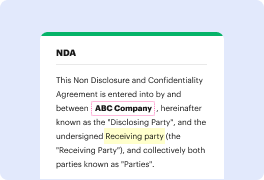
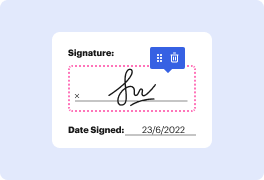
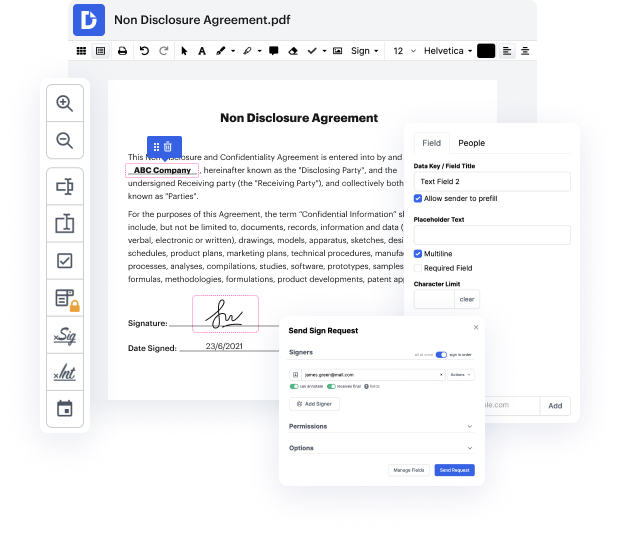
Are you having a hard time finding a trustworthy solution to Exploit Notice For Free? DocHub is designed to make this or any other process built around documents much easier. It's straightforward to explore, use, and make edits to the document whenever you need it. You can access the essential tools for dealing with document-based tasks, like signing, importing text, etc., even with a free plan. Moreover, DocHub integrates with multiple Google Workspace apps as well as solutions, making file exporting and importing a breeze.
DocHub makes it easier to work on paperwork from wherever you’re. Plus, you no longer need to have to print and scan documents back and forth in order to certify them or send them for signature. All the essential tools are at your disposal! Save time and hassle by completing paperwork in just a few clicks. a go today!
In this video tutorial, the presenter introduces three advanced and comprehensive vulnerability scanners: Nuclei for websites and networks, Trivy for container images and GitHub repos, and Vaults for remote scanning of machines and servers. These scanners can detect a wide range of vulnerabilities in various technologies, providing advanced and relevant security measures. The video will demonstrate how to use these scanners effectively to secure both local and remote systems.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



