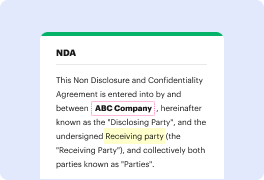
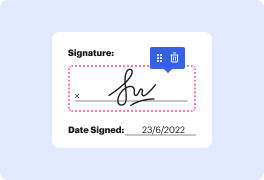
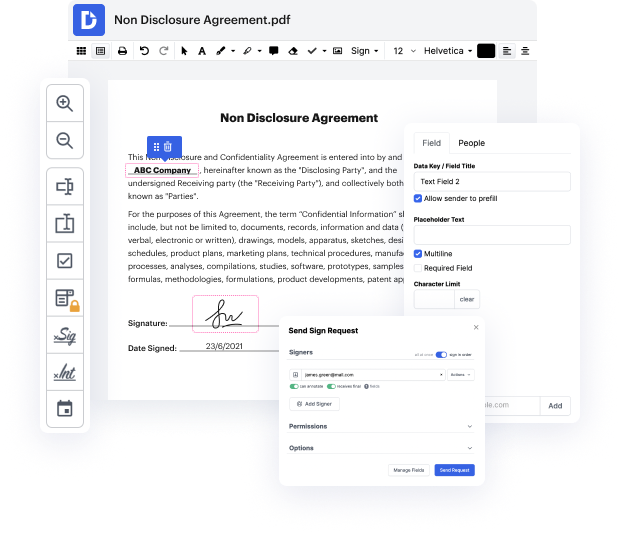
Are you looking for how to Exploit Form For Free or make other edits to a document without downloading any software? Then, DocHub is what you’re after. It's easy, intuitive, and secure to utilize. Even with DocHub’s free plan, you can benefit from its super useful features for editing, annotating, signing, and sharing documents that let you always stay on top of your projects. In addition, the solution provides smooth integrations with Google products, Dropbox, Box and OneDrive, and others, allowing for more streamlined import and export of files.
Don’t spend hours looking for the right solution to Exploit Form For Free. DocHub provides everything you need to make this process as smooth as possible. You don’t have to worry about the security of your data; we adhere to standards in today’s modern world to shield your sensitive data from potential security risks. Sign up for a free account and see how simple it is to work on your documents productively. Try it today!
The tutorial discusses how various hackers can access and leak sensitive information such as usernames, emails, passwords, and credit card details. It explains the process of hacking a website to obtain this data. The key point is understanding the website structure and how users interact with the site. It emphasizes the legality of hacking and the importance of not revealing one's identity if caught. Additionally, the tutorial highlights the use of popular application servers like nginx and apigee for hosting websites and running backend processes. Overall, the tutorial offers a detailed insight into the hacking process and website security vulnerabilities.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



