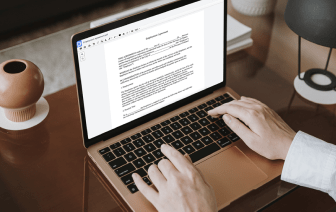
It is usually difficult to get a platform that can deal with all of your corporate needs or offers you appropriate instruments to handle document generation and approval. Choosing an application or platform that includes essential document generation instruments that simplify any task you have in mind is essential. Even though the most popular formatting to work with is PDF, you require a comprehensive software to handle any available formatting, such as NEIS.
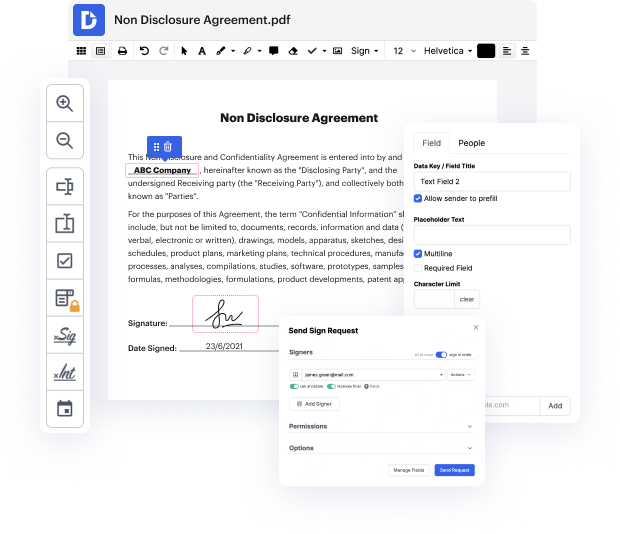
DocHub ensures that all of your document generation needs are taken care of. Modify, eSign, turn and merge your pages in accordance with your preferences with a mouse click. Deal with all formats, such as NEIS, effectively and quickly. Regardless of the formatting you begin working with, it is possible to change it into a needed formatting. Preserve tons of time requesting or looking for the proper document type.
With DocHub, you do not need more time to get familiar with our interface and modifying procedure. DocHub is undoubtedly an easy-to-use and user-friendly software for anybody, even all those with no tech background. Onboard your team and departments and change file administration for your business forever. erase evidence in NEIS, generate fillable forms, eSign your documents, and get processes carried out with DocHub.
Benefit from DocHub’s substantial function list and easily work on any file in any formatting, which includes NEIS. Save time cobbling together third-party platforms and stick to an all-in-one software to enhance your daily processes. Start your free of charge DocHub trial subscription today.
When youre collecting data for evidence, you want to be sure that nothing is going to change with the information that youve collected. One way to ensure this is to create a hash of that data. This is a way to cryptographically verify that what you have collected is going to be exactly the same as what youre examining later. You can think of this as a digital fingerprint. You would take that fingerprint or create that hash when you first collect the data. And then you would verify that hash whenever you perform the analysis to make sure that nothing has changed in the meantime. A relatively simple integrity check can be done with a checksum. This is very commonly done with network communication to make sure that the information that weve sent from one side of the network to the other has shown up without any type of corruption. This isnt designed to replace a hash, but it does provide a simple integrity check that might be useful in certain situations. And we also have to think a