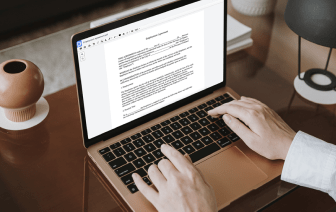
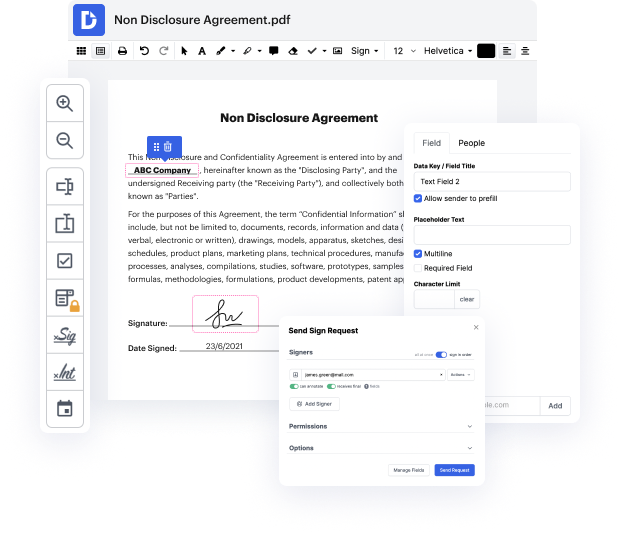
Having full control of your files at any moment is vital to relieve your daily duties and enhance your efficiency. Accomplish any objective with DocHub tools for papers management and hassle-free PDF editing. Access, change and save and incorporate your workflows with other safe cloud storage services.
DocHub provides you with lossless editing, the possibility to use any format, and safely eSign papers without the need of searching for a third-party eSignature option. Make the most from the file managing solutions in one place. Consider all DocHub functions right now with the free of charge account.
In "The Seven Habits of Highly Effective People," Stephen Covey introduces a method for time management through the four quadrants weekly plan, which emphasizes prioritizing tasks. The key questions to define priorities are whether a task is important and whether it is urgent, related to habit three: "Put first things first." Important and urgent tasks include immediate crises like exams, meetings, or emergencies, which demand prompt attention. However, staying in this urgent quadrant for too long can lead to constant stress. Additionally, tasks that are urgent but not important, such as missed phone calls or non-essential requests, can detract from more important responsibilities.