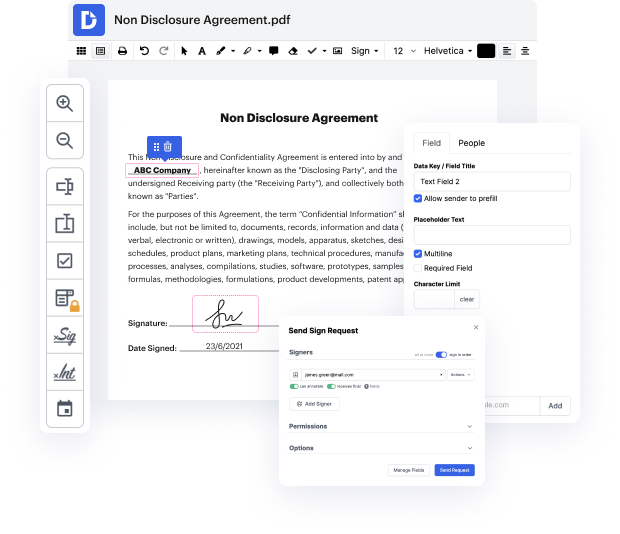
Getting comprehensive power over your documents at any moment is vital to relieve your everyday duties and increase your productivity. Achieve any goal with DocHub tools for document management and hassle-free PDF file editing. Access, change and save and incorporate your workflows along with other safe cloud storage.
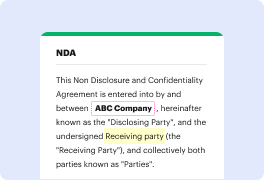
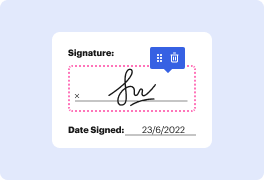
DocHub offers you lossless editing, the chance to work with any formatting, and securely eSign documents without searching for a third-party eSignature alternative. Maximum benefit of the document managing solutions in one place. Consider all DocHub functions today with the free of charge account.
In a recent Instagram post, a user asked about writing a rental contract. Rental contracts vary by jurisdiction, but in Ontario, there's a standard lease that has been in effect since April 2018. This standard form simplifies the agreement between landlords and tenants, ensuring that both parties adhere to a valid contract. Previously, landlords could create contracts at their discretion, leading to potential issues. The standard lease provides clear guidance on what information to include, making the process straightforward. However, complications may arise in specific areas, which could require further attention.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



