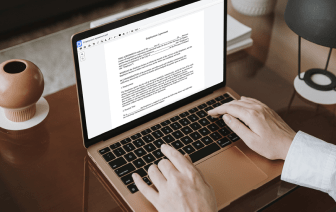
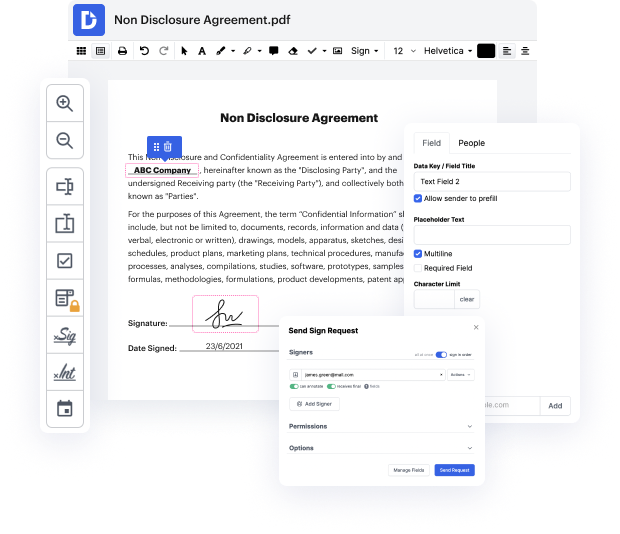
Having complete control of your papers at any time is crucial to alleviate your daily tasks and improve your efficiency. Achieve any objective with DocHub features for document management and practical PDF file editing. Access, adjust and save and incorporate your workflows along with other protected cloud storage services.
DocHub provides you with lossless editing, the opportunity to work with any formatting, and safely eSign documents without searching for a third-party eSignature option. Maximum benefit of your document managing solutions in one place. Consider all DocHub functions today with the free of charge profile.
keeping your text messages protected from hackers and eavesdroppers has become a major issue the government says it occasionally needs access to some of these messages to investigate criminals and terrorists but tech companies see that as a potential violation of privacy your text messages are protected using whats called end-to-end encryption this encryption happens whenever you send a secure text message from your smartphone heres how into end encryption works keep your data private while in transit your phone has two unique keys that encrypt and decrypt messages these are called public and private keys your public key is shared with other people and its used as part of the encryption protocol your private key is only on your device and is never shared when two people want to securely chat they use a combination of public and private keys to create a temporary shared key lets look at how this works Allysons Bob a message which simultaneously causes an exchange of public key bot