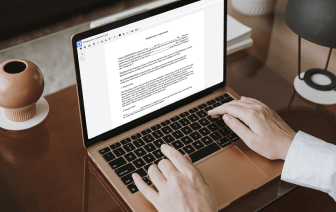
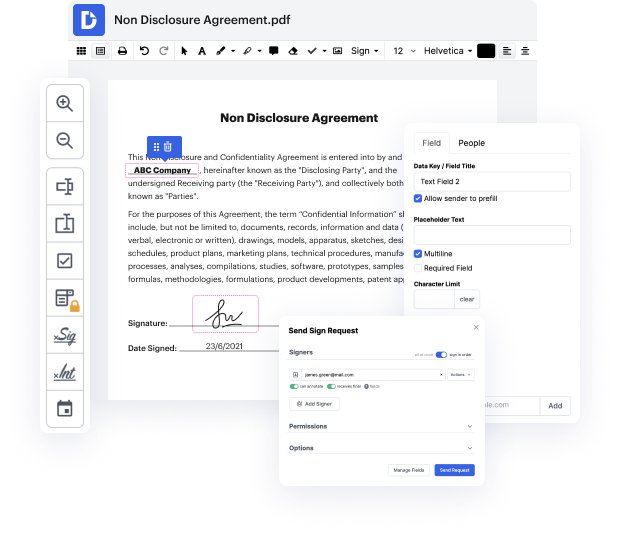
Having full power over your files at any time is crucial to alleviate your everyday duties and improve your productivity. Accomplish any objective with DocHub features for document management and practical PDF editing. Gain access, change and save and incorporate your workflows with other safe cloud storage.
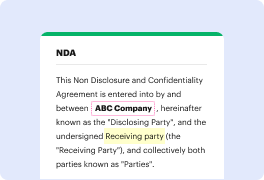
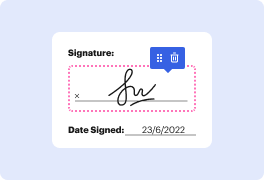
DocHub offers you lossless editing, the opportunity to use any format, and securely eSign documents without looking for a third-party eSignature alternative. Maximum benefit of the document managing solutions in one place. Check out all DocHub capabilities right now with the free account.
In this webinar, Zack Buerkle, VP of the Client Success team at Outmatch, introduces the fourth installment of the summer webinar series focused on their automated reference check tools. The session aims to highlight how this feature enhances the recruiting process by making it faster and more efficient. Drew Morick from the Outmatch Corporate Development team will provide an overview of the reference checking tool. The webinar is designed to be approximately 25 minutes long, allowing participants to gain insight into the platform, with an option for deeper exploration and questions as needed.