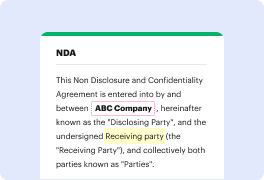
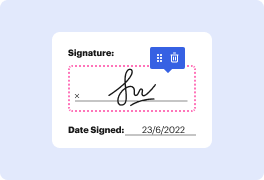
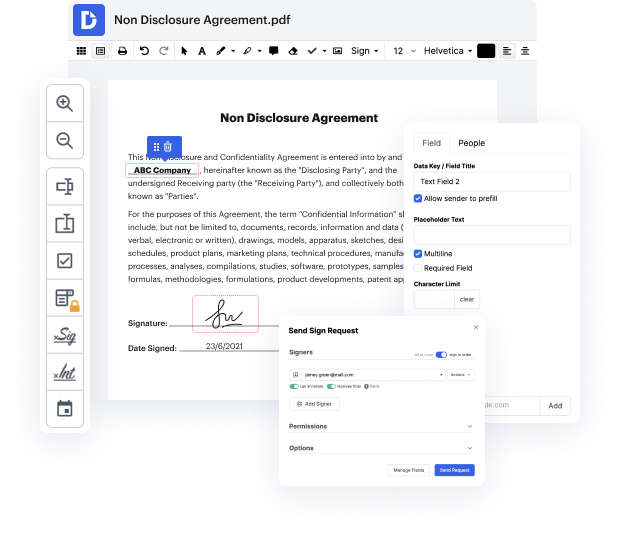
Having comprehensive control of your papers at any moment is important to ease your everyday tasks and enhance your productivity. Achieve any goal with DocHub tools for document management and practical PDF editing. Access, change and save and incorporate your workflows along with other secure cloud storage.
DocHub offers you lossless editing, the possibility to use any format, and safely eSign documents without having looking for a third-party eSignature alternative. Get the most of the file management solutions in one place. Check out all DocHub features today with your free account.
Encryption is the process of scrambling a message so that only authorized individuals can access its contents. There are two main types: symmetric and asymmetric encryption. In symmetric encryption, Alice encrypts a sensitive document with a password and sends it to Bob. However, Bob cannot access the document without knowing the passphrase, creating a dilemma for secure sharing. Sending the passphrase via email poses risks, as it could be intercepted by others. This scenario highlights the challenges of securely sharing keys in symmetric encryption, which leads to the development of asymmetric encryption to address this issue.