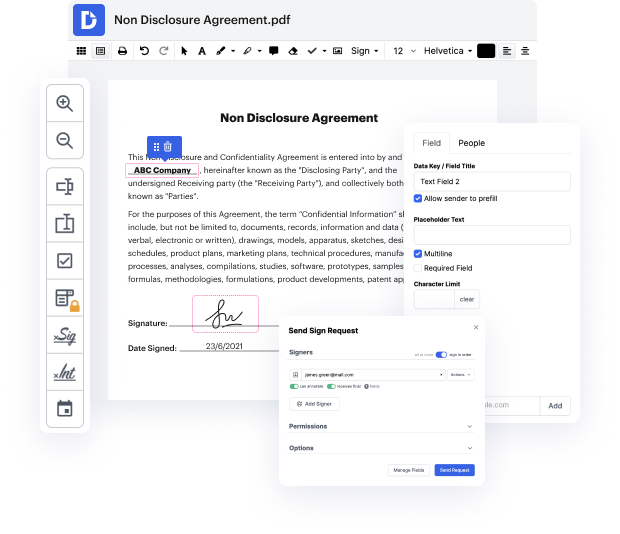
Getting complete power over your documents at any time is vital to ease your daily duties and improve your productivity. Achieve any objective with DocHub features for papers management and practical PDF file editing. Gain access, modify and save and incorporate your workflows along with other secure cloud storage services.
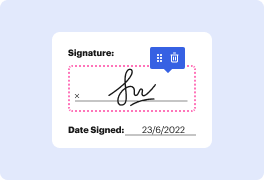
DocHub offers you lossless editing, the possibility to use any format, and safely eSign papers without having searching for a third-party eSignature option. Make the most of the file managing solutions in one place. Check out all DocHub functions right now with the free of charge account.
In this lesson, the focus is on identifying performance under common law and Article 2 of the Uniform Commercial Code (UCC). The discussion transitions from the formation of contracts to performance, examining whether a binding contract (bdocHub) exists. In analyzing a contract law fact pattern, the first step is to determine if there is a traditional enforceable contract by reviewing criteria such as mutual assent, consideration, and any defenses that may invalidate the contract, including scrutiny of the statute of frauds. The session aims to guide viewers in understanding these foundational principles to assess contract performance accurately.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



