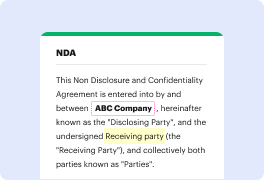
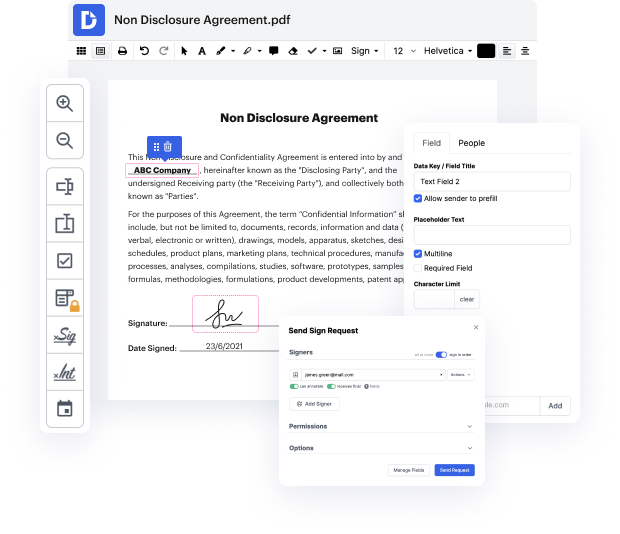
Having complete control of your documents at any moment is essential to alleviate your daily duties and enhance your efficiency. Achieve any objective with DocHub features for papers management and convenient PDF file editing. Access, modify and save and incorporate your workflows along with other safe cloud storage services.
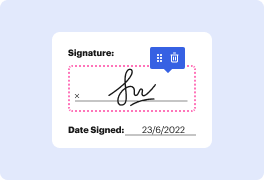
DocHub offers you lossless editing, the opportunity to work with any format, and safely eSign documents without looking for a third-party eSignature option. Get the most from the document management solutions in one place. Consider all DocHub capabilities right now with the free account.
Encryption is a method of scrambling data using a secret key, allowing only authorized organizations to access the original information. It serves as a vital tool for data protection, often mandated by regulations, particularly for sensitive data. Proper key management is crucial; for instance, one wouldn't hide their house key under the mat, as it's the first place thieves would check. Similarly, in data protection, encryption keys must be safeguarded through specialized methods to prevent unauthorized access and ensure the effectiveness of the encryption process.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



