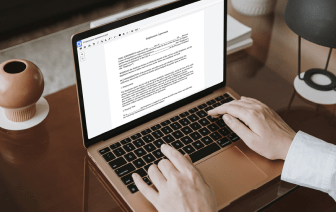

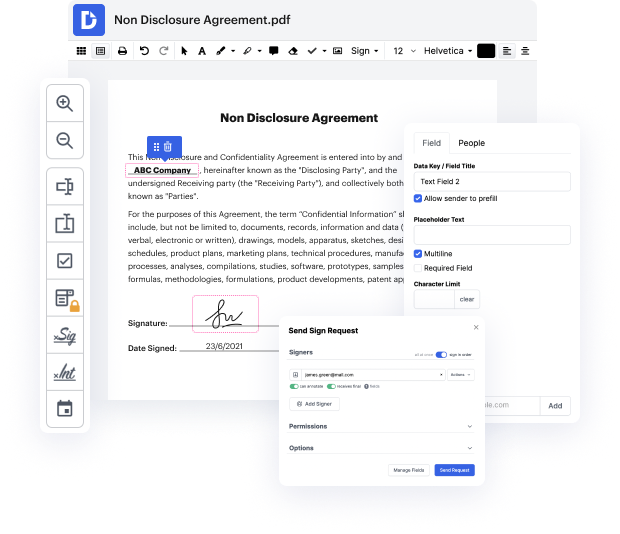
Having comprehensive control of your papers at any time is vital to ease your day-to-day tasks and boost your efficiency. Accomplish any objective with DocHub tools for document management and hassle-free PDF editing. Access, adjust and save and incorporate your workflows along with other safe cloud storage.
DocHub provides you with lossless editing, the opportunity to use any formatting, and securely eSign documents without having looking for a third-party eSignature software. Make the most from the file management solutions in one place. Try out all DocHub features right now with your free account.
In this video, the speaker discusses how encryption works in relation to web communication. He begins by recalling a previous video about DNS and introduces himself as Ethan. The video depicts a scenario where a client machine (represented by Ethan) communicates with a server, which he visualizes with "blinky lights." He explains the concept of a fully qualified domain name that maps to one or more IP addresses and describes the process by which a DNS client requests an IP address from the DNS service. The speaker emphasizes that modern web communication is predominantly encrypted, with a focus on HTTPS as the standard for secure web pages.