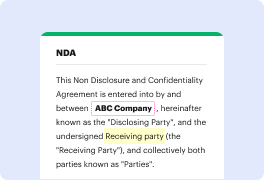
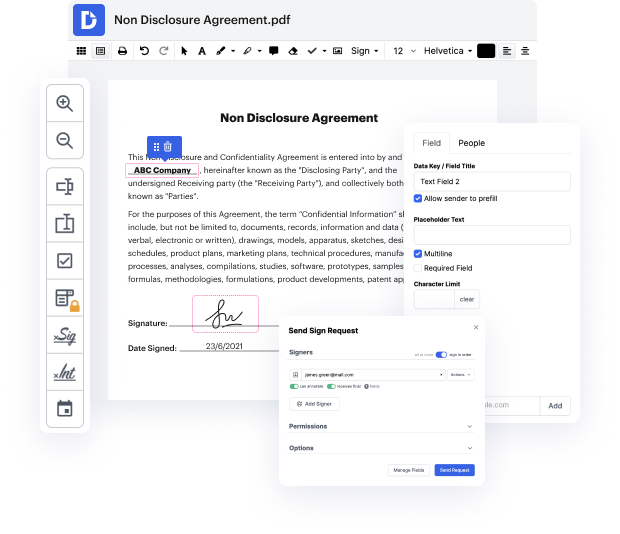
Having full control over your documents at any moment is crucial to relieve your day-to-day duties and improve your efficiency. Accomplish any objective with DocHub tools for papers management and practical PDF editing. Access, change and save and integrate your workflows along with other safe cloud storage.
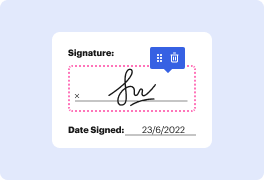
DocHub gives you lossless editing, the chance to work with any formatting, and securely eSign papers without having searching for a third-party eSignature software. Obtain the most of the document managing solutions in one place. Check out all DocHub features today with your free of charge account.
In 2023, encryption has emerged as a vital element in data security, as organizations globally prioritize securing their data. A report based on insights from 4,125 experts reveals trends in encryption strategy adoption, key drivers of encryption, and future trends. It covers features, data types, key management analysis, and high-level views on hardware security module (HSM) deployment options, alongside barriers to adoption. The rise in cyber threats and heightened awareness post-pandemic has prompted approximately 42% of organizations to boost their encryption budgets for FY 22-23, with 65% identifying strong security requirements as a significant driver for these decisions.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



