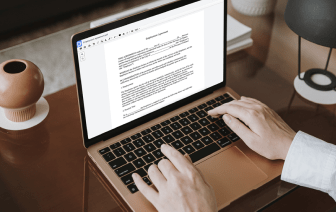
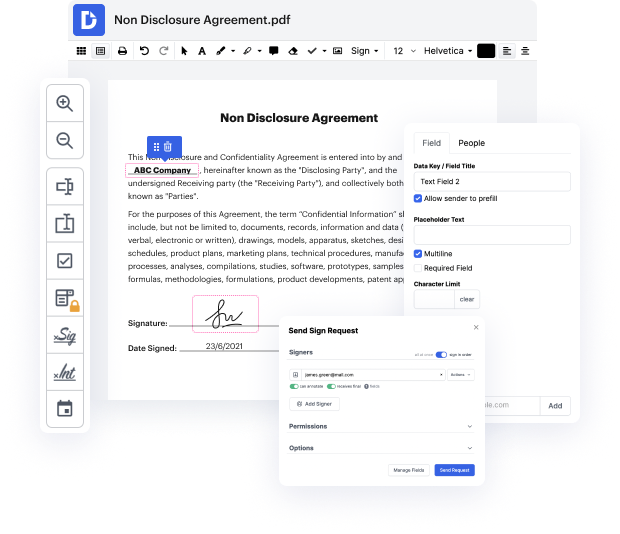
Getting comprehensive control of your documents at any moment is important to alleviate your daily tasks and increase your efficiency. Accomplish any objective with DocHub features for document management and practical PDF file editing. Gain access, modify and save and integrate your workflows along with other secure cloud storage services.
DocHub provides you with lossless editing, the possibility to use any format, and safely eSign documents without the need of looking for a third-party eSignature option. Maximum benefit from the document managing solutions in one place. Consider all DocHub functions today with your free of charge profile.
Encryption scrambles a message's contents, allowing only designated individuals to view it. There are two main types: symmetric and asymmetric encryption. Symmetric encryption involves Alice sending a sensitive document to Bob, encrypted with a password or passphrase. However, Bob cannot access the document without the passphrase, creating a dilemma for Alice on how to share it securely. Sending the passphrase via email is risky, as it could be intercepted by others, potentially allowing them to decrypt communications between Alice and Bob. This issue highlights the limitations of symmetric encryption and the need for a more secure method, which asymmetric encryption addresses.