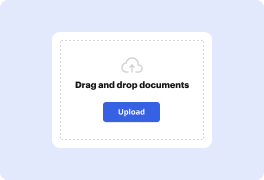
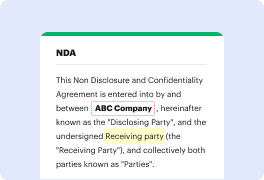
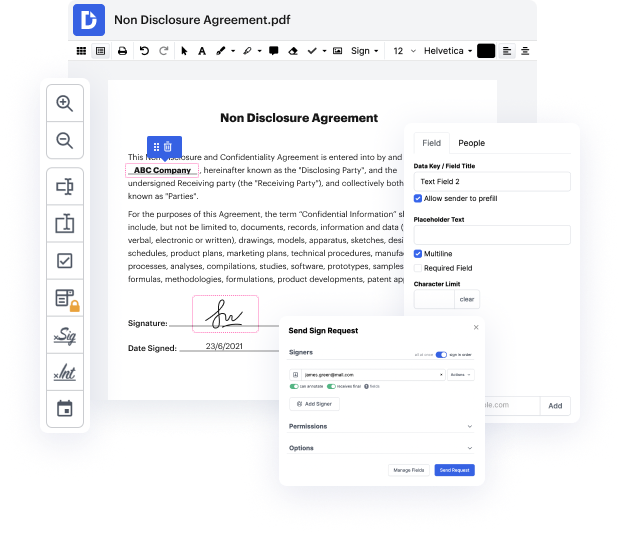
Having comprehensive power over your documents at any time is vital to alleviate your day-to-day tasks and improve your productivity. Accomplish any objective with DocHub tools for document management and practical PDF file editing. Access, change and save and integrate your workflows along with other safe cloud storage.
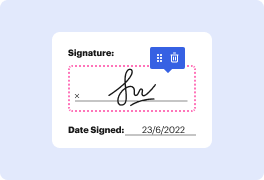
DocHub gives you lossless editing, the possibility to use any format, and safely eSign papers without having looking for a third-party eSignature software. Make the most from the document managing solutions in one place. Check out all DocHub capabilities right now with your free profile.
The video discusses the reasons for using Let's Encrypt, a provider of free security certificates for websites. Let's Encrypt offers automated tools to manage certificates, renewing them every three months. The video provides historical context, noting that during the early internet era, most sites operated without security, primarily using HTTP. HTTPS was mainly utilized by e-commerce sites that required security. The discussion aims to highlight the significance of Let's Encrypt's existence in enhancing web security. It poses the question of whether there are valid reasons to avoid using Let's Encrypt today.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



