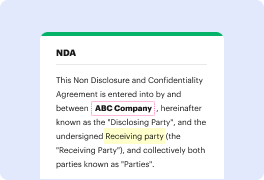
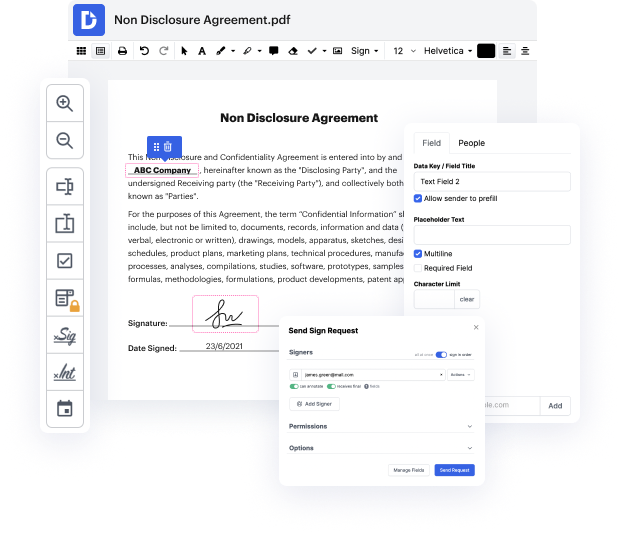
Searching for a specialized tool that deals with particular formats can be time-consuming. Regardless of the huge number of online editors available, not all of them are suitable for Jpeg format, and certainly not all enable you to make changes to your files. To make matters worse, not all of them give you the security you need to protect your devices and documentation. DocHub is a great answer to these challenges.
DocHub is a well-known online solution that covers all of your document editing needs and safeguards your work with enterprise-level data protection. It supports different formats, such as Jpeg, and enables you to modify such paperwork easily and quickly with a rich and user-friendly interface. Our tool complies with important security certifications, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps enhancing its compliance to provide the best user experience. With everything it provides, DocHub is the most reputable way to Embed phone in Jpeg file and manage all of your personal and business documentation, no matter how sensitive it is.
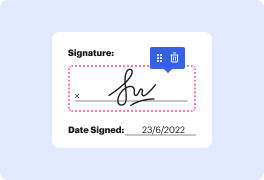
Once you complete all of your adjustments, you can set a password on your updated Jpeg to ensure that only authorized recipients can open it. You can also save your document containing a detailed Audit Trail to see who made what changes and at what time. Choose DocHub for any documentation that you need to edit safely. Sign up now!
hello everyone welcome to Pber Channel recently I have posted a video how to hide exe payload into image so many people has docHubed to me and comment below the video on hacking Android and shoot it like lot of questions on it so thought to answer all your questions by your video and also sharing my experience in research and testing results if you are watching this video without subscribing I would request to subscribe the channel it will really motivate me to do more interesting content for you guys without further delay lets get into the video question 1 how to hide APK payload into image technically you can create a APK payload and compile or compress with image but when I tester in my lab it is not working just image file open but no reverse connection established at the background also I unable to find any proof of concept from the cyber security professional on this please comment below if you have any proof of concept or relevant article let me rese
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



