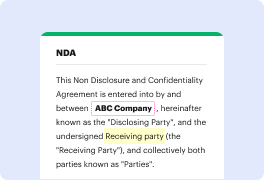
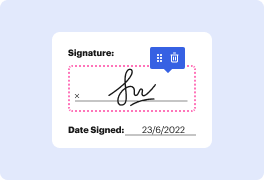
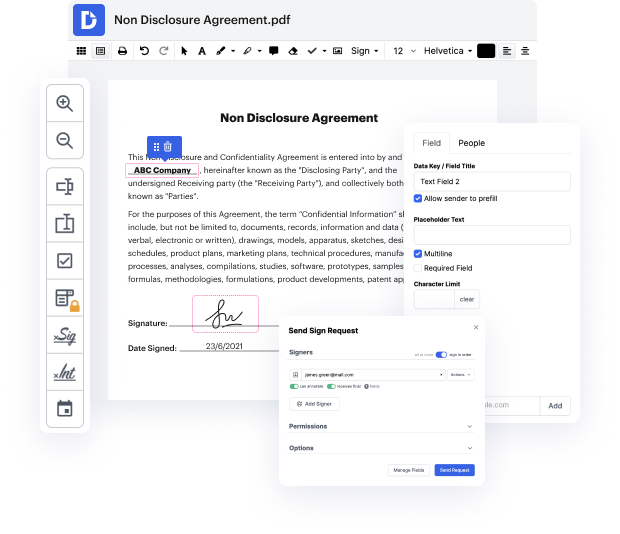
Whether you work with paperwork every day or only occasionally need them, DocHub is here to help you take full advantage of your document-based projects. This platform can embed construction in Security Employment Application, facilitate collaboration in teams and generate fillable forms and legally-binding eSignatures. And even better, every record is kept safe with the highest protection standards.
With DocHub, you can access these features from any location and using any platform.
all right so when I was applying to my first full-time job I sent out a total of 367 cold emails received 21 first round interviews and ended up with five full-time job offers but what those numbers do not show is that most of those interviews only came after I started doing two things first networking my butt off with alumni recruiters and hiring managers and second editing my resume based on their feedback so in this video Ill First share the five biggest resume mistakes I made back in the day then go through the changes that land and meet all those first round interviews lets get started hi friends welcome back to channel if youre new here my name is Jeff Comfort the career tips and stay for the painfully accurate job search memes mistake number one putting the education section above the work experience section while I am still extremely proud of my GP and SAT score recruiters and hiring managers know that any sort of work experience including internships or extracurricular acti
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



