COVID forever changed how organizations look at their internal practices and procedures. It affected organizations of all sizes and sectors, posing new obstacles for staying connected. The pandemic showed that all organizations must integrate digital tools into daily routines. They became essential for far more than hybrid working models.
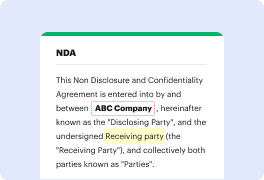
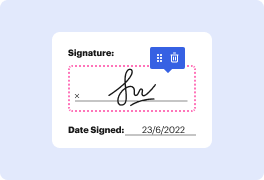
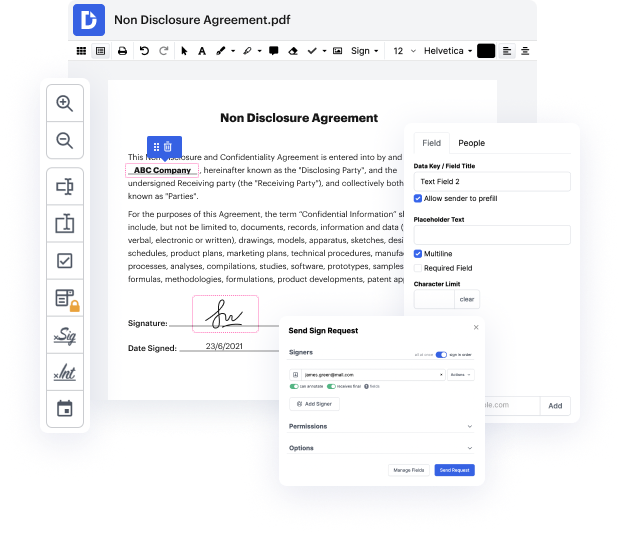
Apps like DocHub allow you to improve your file management and approval procedures. DocHub is the go-to tool for end-to-end online editing and signatures. It helps in reducing your daily contract and agreement generation and approval tasks. Obtain access to Docx Application - Cryptography sophisticated editing tools that cover all your management requires. Deal with any file type and formatting, generate fillable fields, and efficiently gather signatures from your teammates and clients. No previous training or experience is necessary.
With Docx Application - Cryptography, it is possible to maximize the quality of your documents, increase the approval process, and safely store complete documents. Get a cost-free DocHub account right now and change your subscription when you want.
In previous videos, important cryptography concepts were introduced. Hashing functions produce fixed length outputs from any input, providing data integrity. Encryption functions were also discussed, including symmetric algorithms using the same key for encryption and decryption. Secure communication of the encryption key is a challenge.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



