COVID forever altered how organizations look at their internal practices and procedures. It impacted enterprises of all sizes and industries, posing new difficulties for staying connected. The pandemic showed that all organizations need to incorporate digital tools into every day routines. They became essential for far more than hybrid working models.
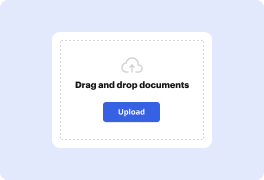
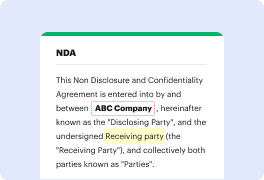
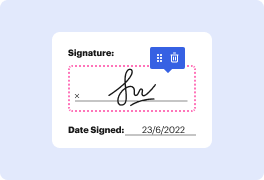
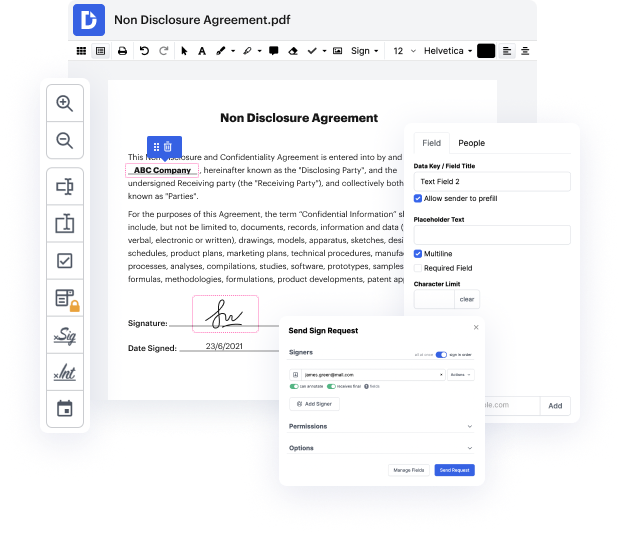
Platforms like DocHub make it easier to boost your document management and approval operations. DocHub is your go-to instrument for end-to-end online editing and signatures. It eases your daily contract and agreement generation and approval tasks. Obtain access to Docx App - SOC advanced editing features which cover all your administration requires. Work with any document type and formatting, make fillable fields, and effectively collect signatures from your teammates and clients. No prior training or experience is required.
With Docx App - SOC, you are able to maximize the quality of your documents, boost the approval process, and securely store finished documents. Get yourself a cost-free DocHub profile today and change your subscription when ready.
Autonomic Security Operations (ASO) is a framework developed by Google Cloud to help customers enhance their security operations by utilizing commercial capabilities, modern operating models, and powerful tools like the Chronicle Security Operations Suite. The goal is to bridge the gap between Google's engineering capabilities and what customers can achieve with these technologies. ASO focuses on setting up organizations for success, addressing strategic questions, achieving operational efficiency, and improving detection and response efficacy.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



