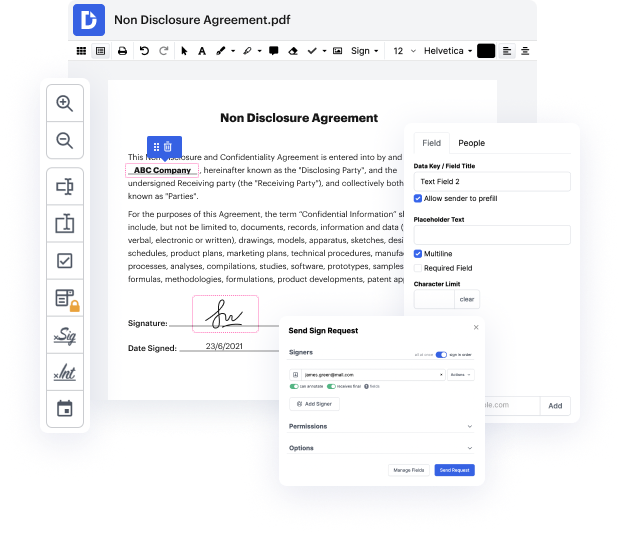
Keeping up with the fast-changing work environment that has emerged because COVID continues to be a significant aspect for a lot of sectors. Many organizations look for an accessible and easy-to-adopt platform that will be available for them 24/7. The key interest is based on addressing all file generation and approval procedures with minimum time and effort. DocHub provides powerful features and storage space integrations that can boost your every day file operations forever. You only need a free DocHub profile to access Document Editor - Digital Certificate.
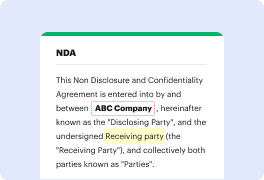
DocHub is an end-to-end editing and annotation platform that addresses all of your document generation demands. Make documents from scratch, change them, leave feedback, and swiftly collect signatures from teammates and clients. Forget about losing your documents or worrying for their security - DocHub has industry-leading security standards that shield your data.
Focus on agreements and contracts anyplace, at any time. Get the most from Document Editor - Digital Certificate and increase your every day file managing, from file creation to approval and storage space.
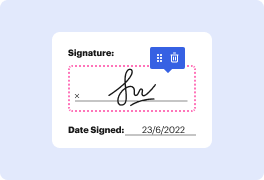
Digital signatures use symmetric key cryptography. In this system, one key is used to encrypt a message, and only the other key can decrypt it. To send a secret message, a pair of mathematically related keys is needed. One key is sent to the recipient, while the other is kept private. The recipient uses the public key to encrypt a message, and only they can decrypt it using the private key. This ensures secure communication between parties.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



