COVID forever transformed how organizations look at their internal protocols and procedures. It affected organizations of all sizes and industries, posing new challenges for staying connected. The pandemic demonstrated that all organizations should integrate digital instruments into daily routines. They became crucial for far more than hybrid working models.
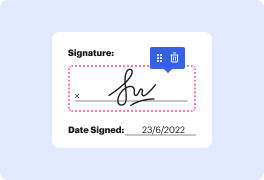
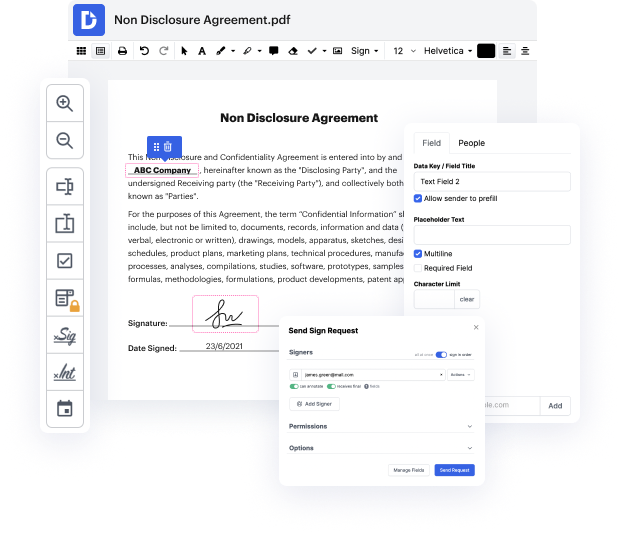
Apps like DocHub allow you to increase your document management and approval procedures. DocHub is the go-to instrument for end-to-end online editing and signatures. It helps reduce your day-to-day contract and agreement generation and approval tasks. Get access to Document Application - SOC-2 sophisticated editing features that cover all of your management requires. Deal with any document type and format, make fillable fields, and efficiently gather signatures from your teammates and customers. No past training or experience is needed.
With Document Application - SOC-2, it is possible to increase the quality of your files, accelerate the approval process, and safely store finished files. Obtain a cost-free DocHub account right now and change your subscription when ready.
the original standard was known as SAS 70 statement on auditing standards which in 2011 was replaced by sock to service organizational controls - this was developed in America and by the American Institute of Certified Public Accountants sagt who defines the criteria for managing customers data based on the five service principles security availability processing integrity confidentiality and privacy unlike PCI DSS which has very rigid security control requirements - reports are unique to each organization these are in line with specific business practices Eve designs its own controls to comply with one or more of the trust principles first is security the security principle refers to the protection of system resources against unauthorized access access controls help prevent potential system abuse theft or unauthorized removal of data misuse of software and improper alteration or disclosure of information IT security tools such as network and web application firewalls two-factor authe
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



