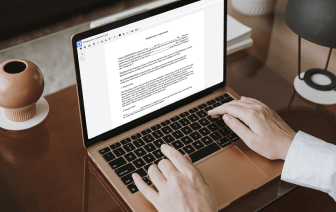
Unusual file formats in your day-to-day papers management and editing processes can create instant confusion over how to edit them. You might need more than pre-installed computer software for efficient and speedy document editing. If you want to delete stamp in LOG or make any other simple alternation in your document, choose a document editor that has the features for you to deal with ease. To handle all of the formats, including LOG, opting for an editor that works well with all kinds of documents will be your best choice.
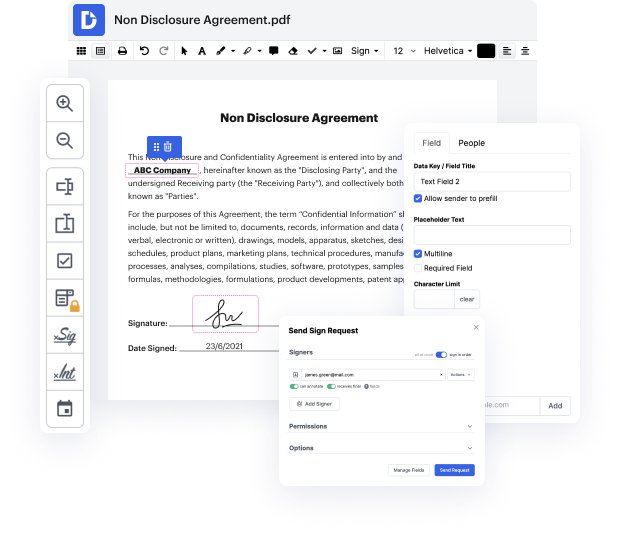
Try DocHub for efficient document management, regardless of your document’s format. It offers potent online editing instruments that streamline your papers management process. You can easily create, edit, annotate, and share any document, as all you need to gain access these features is an internet connection and an functioning DocHub profile. A single document tool is everything required. Don’t lose time switching between different programs for different documents.
Enjoy the efficiency of working with an instrument made specifically to streamline papers processing. See how easy it really is to modify any document, even when it is the very first time you have worked with its format. Sign up an account now and enhance your entire working process.
[Music] hey guys hackersploit here back again with another video and in this video ill be showing you how to clear your tracks on linux operating systems with a variety of tools all right so why is this important now if youre a penetration tester you probably already know why this is important well covering tracks or clearing your tracks is the final stage of penetration of the penetration testing process so just before you start report writing and that video is on its way by the way so do stay tuned for that so clearing your tracks essentially involves clearing or wiping all the activity of an attacker or you being the attacker that is so as to avoid any detection by incident response teams or forensic teams all right so it is vitally important in the penetration testing life cycle and of course if you look at it from a defensive point of view it can really test incident handlers and the blue team in their ability to discover an attacker in in the system whether they do have an int