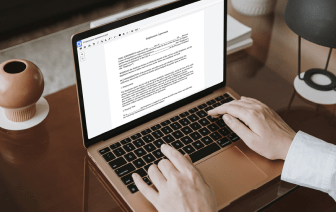

Document generation and approval are a key priority for each firm. Whether handling large bulks of files or a specific agreement, you must remain at the top of your efficiency. Finding a ideal online platform that tackles your most typical file creation and approval challenges might result in quite a lot of work. Many online apps offer you merely a minimal list of editing and eSignature capabilities, some of which might be valuable to handle NEIS file format. A solution that handles any file format and task might be a exceptional choice when choosing program.
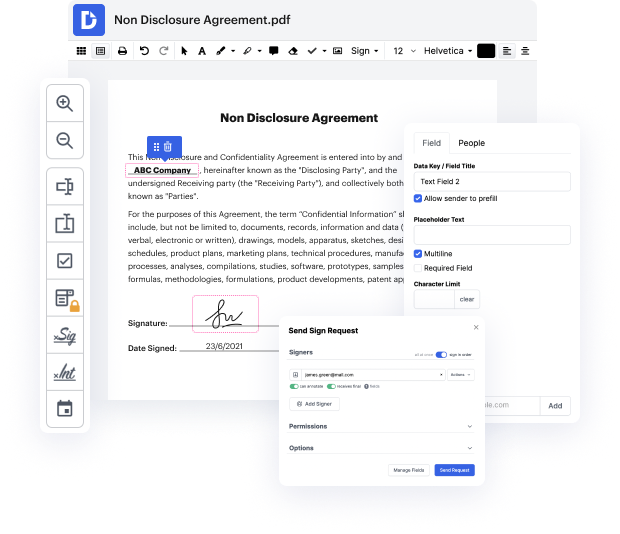
Take document managing and creation to a different level of simplicity and sophistication without picking an cumbersome interface or expensive subscription plan. DocHub offers you tools and features to deal successfully with all of document types, including NEIS, and execute tasks of any difficulty. Change, arrange, and make reusable fillable forms without effort. Get total freedom and flexibility to delete secret in NEIS at any moment and safely store all of your complete documents within your user profile or one of many possible integrated cloud storage apps.
DocHub offers loss-free editing, eSignaturel collection, and NEIS managing on the expert level. You don’t need to go through exhausting guides and spend a lot of time finding out the platform. Make top-tier secure document editing an ordinary process for your daily workflows.
[Music] [Applause] [Music] hello Im Thai a cloud support engineer here at the AWS office in Dublin today Im going to show you how to immediately delete a secret manager secret so that you can create a new secret with the same name lets get started when you delete the secret Secrets manager doesnt immediately delete the secret instead secret manager immediately makes the secret inaccessible and scheduled for deletion after a recovery window of a minimum of 7 days this means that you cannot recreate a secret using the same name using the AWS Management console until the recovery window ends however you can permanently delete a secret without any recovery window using the AWS command line interface after logging into the AWS Management console navigate to the secrets manager console in the console you can see a list of secrets in your account to see secrets that are scheduled for deletion choose the settings icon and then in preferences select show Secrets scheduled for deletion invi