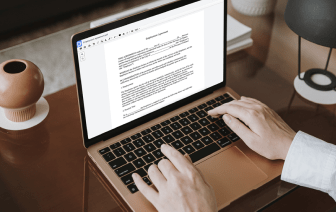
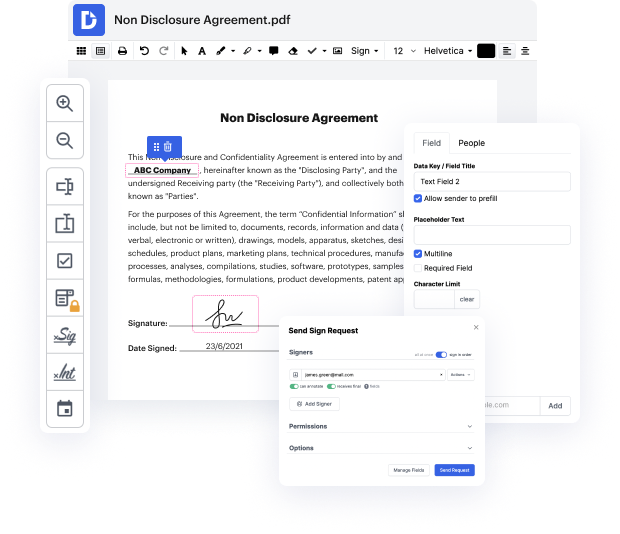
No matter how complex and difficult to modify your files are, DocHub provides an easy way to change them. You can change any part in your 602 without extra resources. Whether you need to tweak a single element or the whole form, you can rely on our powerful solution for fast and quality results.
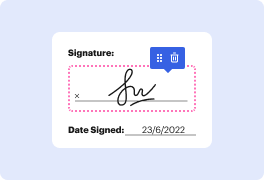
Additionally, it makes sure that the final document is always ready to use so that you’ll be able to get on with your projects without any delays. Our all-encompassing set of features also features pro productivity features and a library of templates, allowing you to make the most of your workflows without the need of wasting time on repetitive operations. In addition, you can access your documents from any device and incorporate DocHub with other solutions.
DocHub can take care of any of your form management operations. With a great deal of features, you can create and export paperwork however you want. Everything you export to DocHub’s editor will be stored securely for as long as you need, with rigid protection and information protection frameworks in place.
Try out DocHub now and make handling your paperwork more seamless!
Wars are always destructive and their results are often elusive. But no other struggle quite underlies the short-sightedness and unfruitful nature of fighting as well as the Byzantine-Sasanian War of 602 to 628. Neither empire gained much through this long conflict and the war allowed a completely new power, Islam, to become dominant in the region. Welcome to the new edition of Kings and Generals, the documentary series. Since the disastrous Battle of Carrhae in 53 BC, the Romans and Persians fought in countless conflicts until a certain balance formed between them. Neither side was ever able to strike a final blow against its long-standing enemy. The new hostilities started in 571. The Sassanidsamp;#39; Arab clients, the Lakhmids, attacked Byzantiumamp;#39;s Arab clients, the Gassanids in 570 and then the Persians invaded Yemen and expelled the Byzantine allies from there. The Romans attempted to incite revolts against the Sasanians in modern-day Georgia and Armenia and eventually o