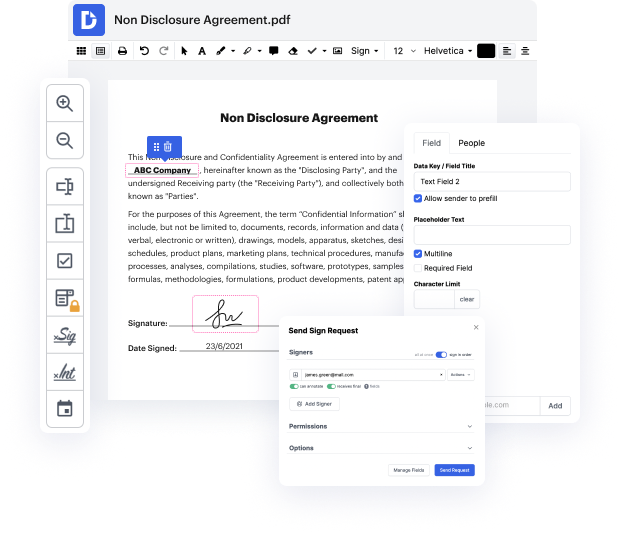
You no longer have to worry about how to cover up URL in EGT. Our comprehensive solution guarantees easy and quick document management, allowing you to work on EGT files in a few minutes instead of hours or days. Our service covers all the tools you need: merging, inserting fillable fields, approving documents legally, inserting shapes, and so on. There’s no need to install extra software or bother with expensive programs demanding a powerful computer. With only two clicks in your browser, you can access everything you need.
Start now and manage all different types of files professionally!
in a previous video we talked about how fishing attack unrolls step by step from the initial access through either email or text message or phone call into either URL attachment and then potentially added into malware explore it or fishing website we also covered how different techniques like a type of squatting or abusing subdomain or URL path used by attacker to try to imitate a benign URL inside official benign domain inside the fusion URL today weamp;#39;re going to talk about more Advanced Techniques which would most likely used in a target attack to actually completely hide a phishing URL and make it look like a legitimate one an exact copy of legitimate URL to fool a victim to believe that the victim is visiting a legitimate website sometimes especially in in a target attack in a spearfishing an attacker cannot afford to play by chance so they want the URL to look exactly like a benign website thereamp;#39;s a couple of techniques published by the security researcher with the