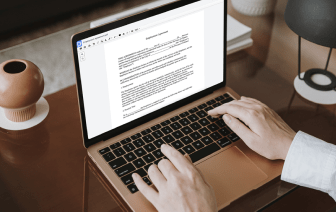
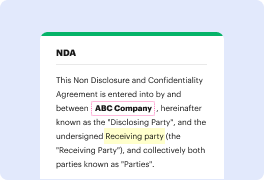
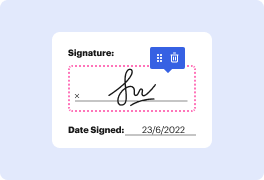
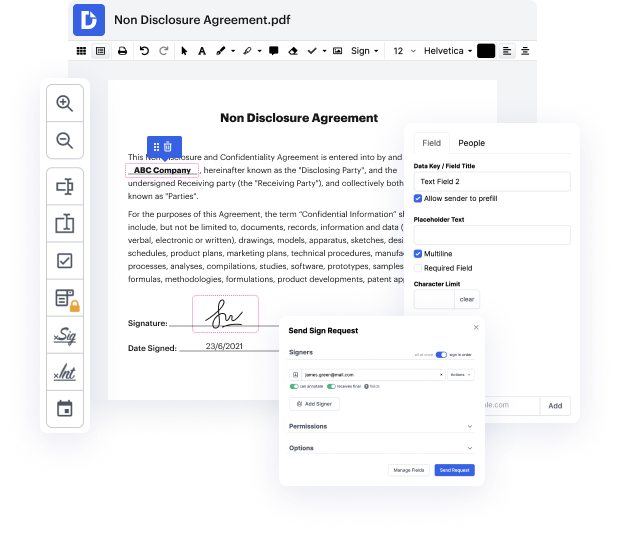
DocHub makes it fast and simple to cover up detail in LOG. No need to instal any extra application – simply add your LOG to your profile, use the easy drag-and-drop interface, and quickly make edits. You can even use your computer or mobile device to adjust your document online from anywhere. That's not all; DocHub is more than just an editor. It's an all-in-one document management platform with form building, eSignature features, and the option to let others complete and eSign documents.
Each file you upload you can find in your Documents folder. Create folders and organize records for easier search and retrieval. In addition, DocHub ensures the security of all its users' information by complying with stringent security standards.
naima abdullah he following this from the newsroom thatamp;#39;s right heamp;#39;s just 18 years old and arrested for all the pricey fraudulent transactions he allegedly made Charles Turneramp;#39;s alleged crimes finally came to an end yesterday when sales put Fulton Police and the Georgia Department of Revenue searched the teamamp;#39;s home weamp;#39;re told the crimes happened online and at several South Fulton banks amounting to 28 million dollars authorities say Turner got the money by overpaying with his holding account for a business he created and then tried to get a refund from the Georgia Department of Revenue now Turner as weamp;#39;re learning was also wanted on a warrant for alleged forgery and now heamp;#39;s arrested with these new job with these new charges sitting in jail Sheba