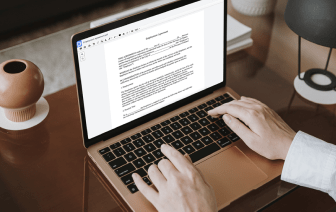
Browsing for a professional tool that deals with particular formats can be time-consuming. Regardless of the vast number of online editors available, not all of them are suitable for 602 format, and definitely not all enable you to make modifications to your files. To make things worse, not all of them provide the security you need to protect your devices and paperwork. DocHub is a great answer to these challenges.
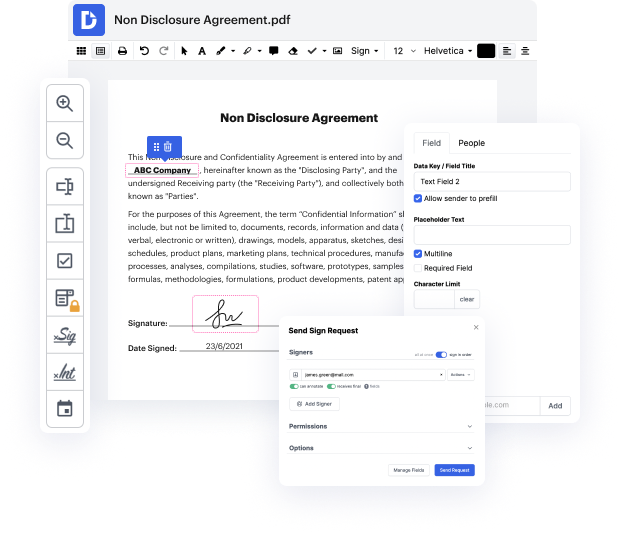
DocHub is a well-known online solution that covers all of your document editing requirements and safeguards your work with enterprise-level data protection. It supports different formats, including 602, and helps you edit such paperwork quickly and easily with a rich and user-friendly interface. Our tool meets crucial security standards, like GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to guarantee the best user experience. With everything it provides, DocHub is the most reputable way to Correct authentication in 602 file and manage all of your individual and business paperwork, irrespective of how sensitive it is.
After you complete all of your modifications, you can set a password on your updated 602 to ensure that only authorized recipients can work with it. You can also save your paperwork with a detailed Audit Trail to find out who applied what changes and at what time. Select DocHub for any paperwork that you need to edit securely. Subscribe now!
When youre connecting to a wireless network. One of the first thing that happens is authentication. We need some way to ensure that the people connecting to the wireless network are truly authorized to be on that wireless network. This could be a wireless network thats configured to allow access for mobile users. Or this may be in a coffee shop where the people stopping by are simply there temporarily and then they leave the network. There are generally two major ways to authenticate to a wireless network. The first is giving everyone the same password. We refer to this as a pre-shared key because weve created the key previously. And then we hand that key out to anyone who needs access to the network. These pre-shared keys or shared passwords are commonly used for networks that we might have at our home. In our corporate environment however, we need additional security. We need to make sure that everyone has a different authentication method for logging in. We want to be sure that i