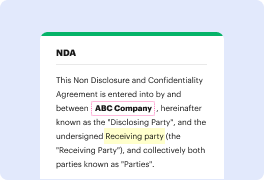
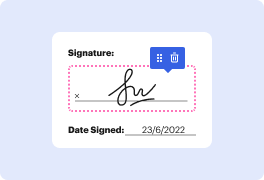
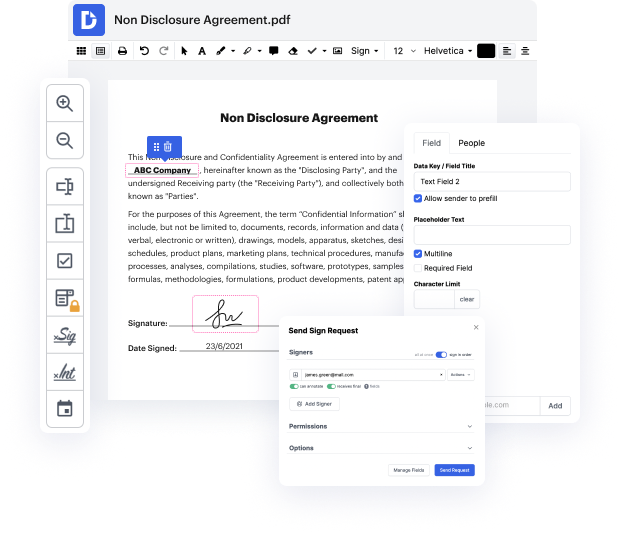
DocHub is an all-in-one PDF editor that allows you to conceal PII in INFO, and much more. You can underline, blackout, or remove paperwork fragments, add text and pictures where you need them, and collect data and signatures. And since it runs on any web browser, you won’t need to update your software to access its powerful capabilities, saving you money. When you have DocHub, a web browser is all it takes to handle your INFO.
Sign in to our website and adhere to these instructions:
It couldn't be easier! Enhance your document management now with DocHub!
today weamp;#39;re going to look at using dynamic data masking and snowflake to handle this use case human resources has the following requirements around personally identifiable information their employee salary data and there are these four requirements a regular employee is allowed to see his or her own data a manager can see data related to his or her direct and indirect reports and members of hr can see everybodyamp;#39;s data except for other hr people members of finance can see data rolled up by department now how can we implement this in snowflake using dynamic data masking and how can we also use this to implement row level security so that users can only see the records that they are authorized now let me so weamp;#39;re going to walk through this demo and do these four different scripts and this is inspired by this uh article this blog by vlad vlad valeev at electronic arts and this all of the code that is used here is at this github it will also be in the description of