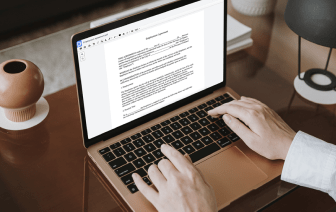
When you edit documents in various formats daily, the universality of your document tools matters a lot. If your tools work for only some of the popular formats, you may find yourself switching between application windows to conceal picture in NEIS and handle other file formats. If you want to take away the headache of document editing, go for a platform that can effortlessly manage any format.
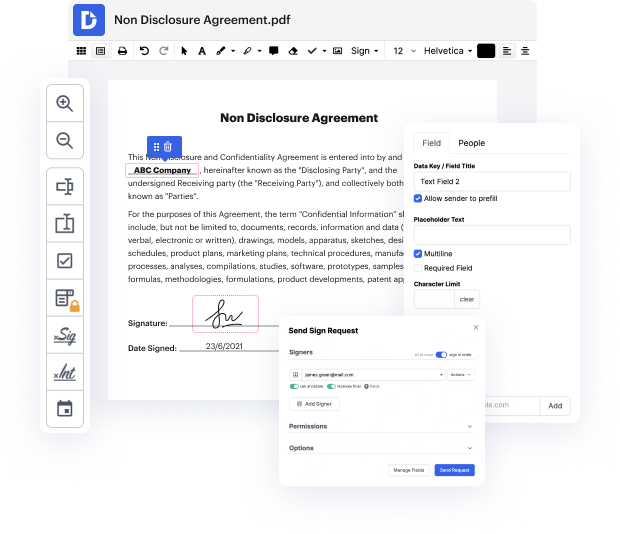
With DocHub, you do not need to concentrate on anything apart from actual document editing. You won’t have to juggle programs to work with diverse formats. It will help you modify your NEIS as effortlessly as any other format. Create NEIS documents, edit, and share them in a single online editing platform that saves you time and boosts your productivity. All you need to do is register a free account at DocHub, which takes only a few minutes or so.
You won’t need to become an editing multitasker with DocHub. Its functionality is sufficient for speedy document editing, regardless of the format you want to revise. Begin with creating a free account and discover how easy document management may be having a tool designed specifically to meet your needs.
[Music] what is going on guys welcome back in todays video were going to learn how to hide information inside of jpeg files and this goes beyond basic stuff like strings numbers or any other primitive data types were going to be able to hide fully executable programs inside of jpeg files without changing the image without changing anything about the image functionality its still a normal photo its still a normal jpeg file but it has some information in it that we can then also extract again and in order to show you how you can do that were going to use this image here so this is a basic jpeg file an image of a woman taking a picture with a camera and all that uh you can see the extension here is jpeg literally every jpeg file that is a normal jpeg file will work for this so you dont have to pick a special one um and were going to look at the bytes of the jpeg file in order to see why we can do that and how we can do that now in order to look at the bytes were not going to use