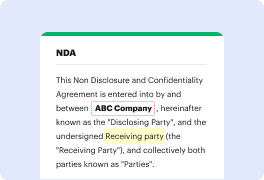
Unusual file formats within your everyday papers management and editing operations can create immediate confusion over how to modify them. You might need more than pre-installed computer software for efficient and speedy document editing. If you want to conceal phone number in jpg or make any other basic alternation in your document, choose a document editor that has the features for you to deal with ease. To handle all the formats, including jpg, opting for an editor that actually works properly with all types of files is your best option.
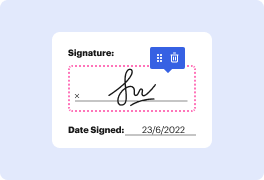
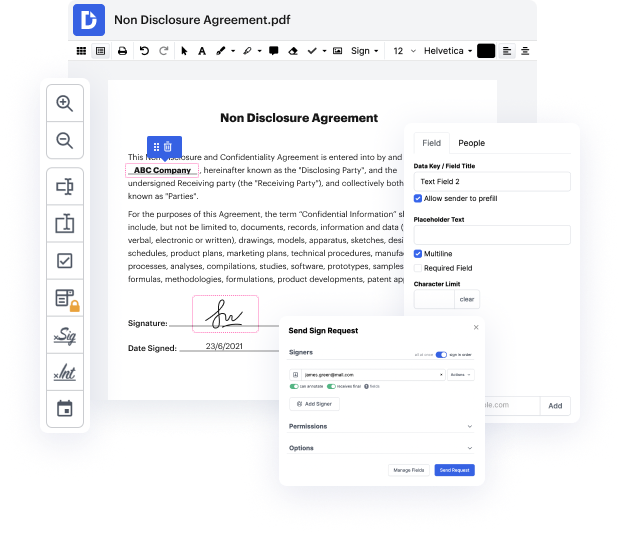
Try DocHub for efficient document management, regardless of your document’s format. It has potent online editing instruments that streamline your papers management process. It is easy to create, edit, annotate, and share any file, as all you need to access these characteristics is an internet connection and an active DocHub account. Just one document tool is all you need. Don’t waste time switching between various programs for different files.
Enjoy the efficiency of working with a tool created specifically to streamline papers processing. See how easy it is to edit any document, even if it is the very first time you have worked with its format. Register an account now and enhance your entire working process.
if youve been curious about the hacker applications of steganography today well show you a technique to hide and then execute a payload in an image file on this episode of cyberweapons lab [Applause] [Music] steganography is a practice of hiding things in an image and in previous episodes weve covered how to do this but today were going to take it a step further and actually attempt to execute code that weve hidden inside an image now why might we want to do this well there are actually instances of botnets being controlled by checking a twitter feed and then downloading an image that controls hidden command tags and this is interesting because typically the way that a malware researcher would find something like this is by focusing on the communication between the command and control server and infected computers by instead directing the traffic to a public ip address like twitter youd be able to get around your ip getting flagged and all your bots getting taken down which is a
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



