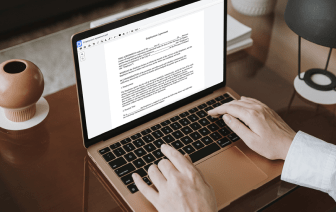
When you edit files in various formats daily, the universality of your document solution matters a lot. If your instruments work with only some of the popular formats, you might find yourself switching between application windows to conceal information in LOG and manage other document formats. If you want to remove the hassle of document editing, get a platform that can easily handle any extension.
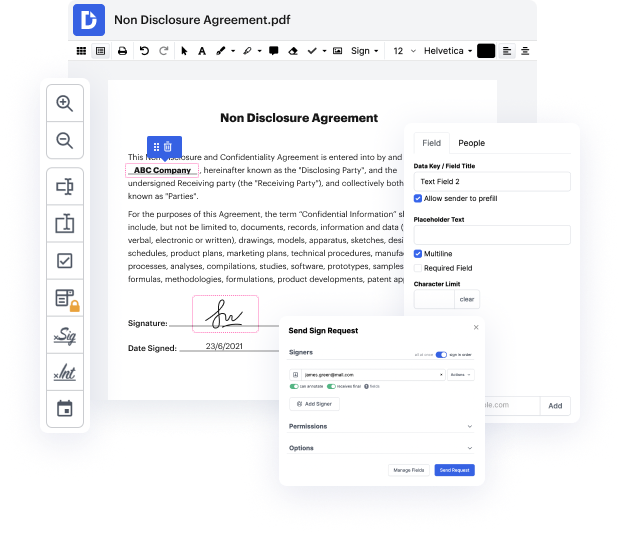
With DocHub, you do not need to concentrate on anything but actual document editing. You won’t have to juggle applications to work with various formats. It can help you modify your LOG as easily as any other extension. Create LOG documents, edit, and share them in one online editing platform that saves you time and boosts your efficiency. All you have to do is sign up an account at DocHub, which takes just a few minutes or so.
You won’t need to become an editing multitasker with DocHub. Its feature set is enough for speedy document editing, regardless of the format you need to revise. Start by registering an account and discover how straightforward document management can be having a tool designed particularly to suit your needs.
hello everyone welcome back to the linux linux server security series in this video we are going to be taking a look at logging and system monitoring on linux now its its very important to understand the context in which well be looking at this because uh when we talk about things like logging on linux uh this uh this can be quite a complicated an advanced topic uh given the various uh the various forms of logs that are going to be collected on a linux system so we are primarily going to be interested with the security logs or logs related to security events on the system uh um we are then going to be taking a look at monitoring your system so uh analyzing the various processes that are currently running on the system i will take a look at how to monitor user activity on a system and how to view what each user is doing so on and so forth so to begin with uh we have already taken a look at on a very basic level how our logs are used on linux in regards to security events for example