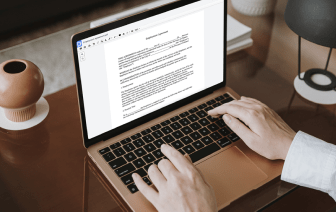
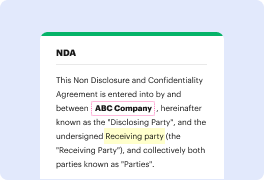
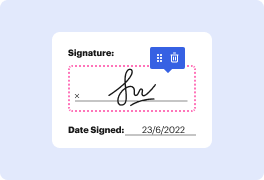
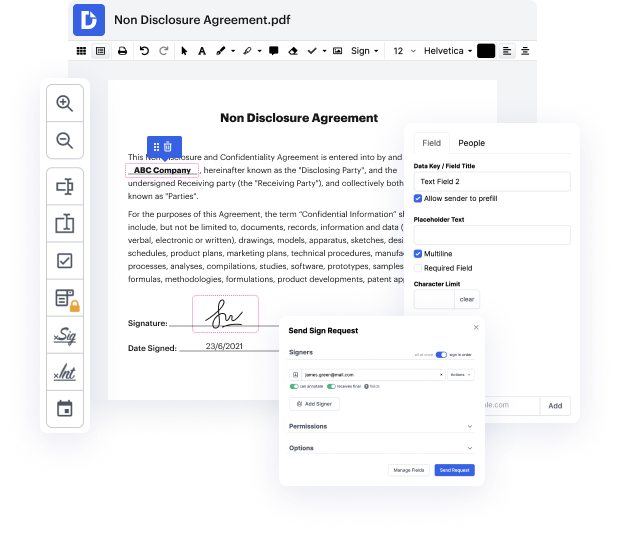
DocHub makes it quick and straightforward to conceal data in LOG. No need to download any extra application – simply upload your LOG to your profile, use the easy drag-and-drop interface, and quickly make edits. You can even use your PC or mobile device to adjust your document online from anywhere. That's not all; DocHub is more than just an editor. It's an all-in-one document management platform with form constructing, eSignature capabilities, and the ability to allow others fill in and eSign documents.
Each file you upload you can find in your Documents folder. Create folders and organize records for easier search and access. Furthermore, DocHub guarantees the security of all its users' data by complying with stringent protection protocols.
here Iamp;#39;m going to show you how to make it easier to focus on certain parts of your workbook without having to export those parts so how to hide data here and there so you can send it to your co-worker and have them only focus on what you want them to see and Iamp;#39;m going to show you three simple robust tips for them so here we have a nice workbook with a few tabs but I only want the user letamp;#39;s say here on this tab to focus on one chart now letamp;#39;s say that you have a lot of charts is there an easy way to make it so they only focus on this one right here well yes there is and that is tip one so we want to go to the page layout tab and then we can go and click selection pane and this is going to show you all of the objects here that we can show and hide and there are quite a lot of them but the ones called chart are going to be for our charts so letamp;#39;s say that we donamp;#39;t want to show this one down here we can click the little I right here and the