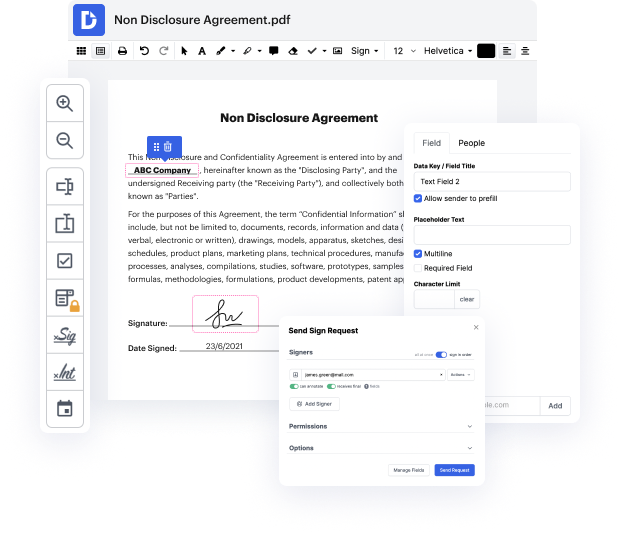
People frequently need to conceal authentication in LOG when working with forms. Unfortunately, few applications offer the options you need to accomplish this task. To do something like this normally requires switching between several software packages, which take time and effort. Luckily, there is a solution that works for almost any job: DocHub.
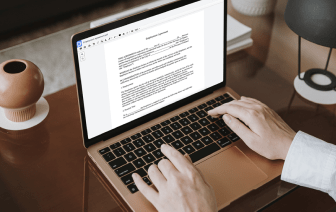
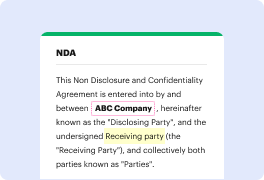
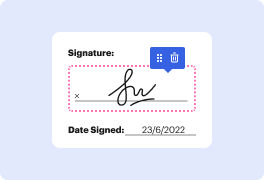
DocHub is a perfectly-developed PDF editor with a full set of valuable functions in one place. Altering, approving, and sharing documents is easy with our online solution, which you can use from any internet-connected device.
By following these five simple steps, you'll have your revised LOG quickly. The intuitive interface makes the process quick and productive - stopping switching between windows. Try DocHub now!
in this tutorial Iamp;#39;m going to show you to use WPS hide login which is a plugin that allows you to change the URL of your login page now you may or may not know this but hackers use BOTS to try to brute force websites and most WordPress websites have the login page at the same location which is their domain name forward slash WP dash login dot PHP this plugin allows us to change that URL or that slug to anything whatever we want so itamp;#39;d be your domain forward slash whatever you want and the bots donamp;#39;t know what that is itamp;#39;s not linked to from anywhere on your site hopefully whether or not thatamp;#39;s true depends on your theme but either way weamp;#39;re gonna hide the login page and weamp;#39;re getting started right now whatamp;#39;s up guys welcome back to the video to be orange from the WP Learning Lab where we help you get better at WordPress so you can earn more for yourself for your clients and for your business if itamp;#39;s your first tim