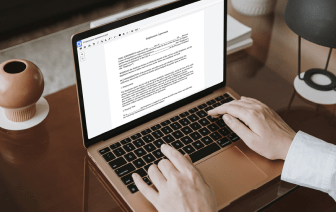

When your daily tasks scope includes a lot of document editing, you already know that every file format requires its own approach and in some cases specific software. Handling a seemingly simple LOG file can sometimes grind the whole process to a stop, especially if you are trying to edit with inadequate tools. To prevent such problems, find an editor that can cover all of your needs regardless of the file extension and clean theme in LOG with zero roadblocks.
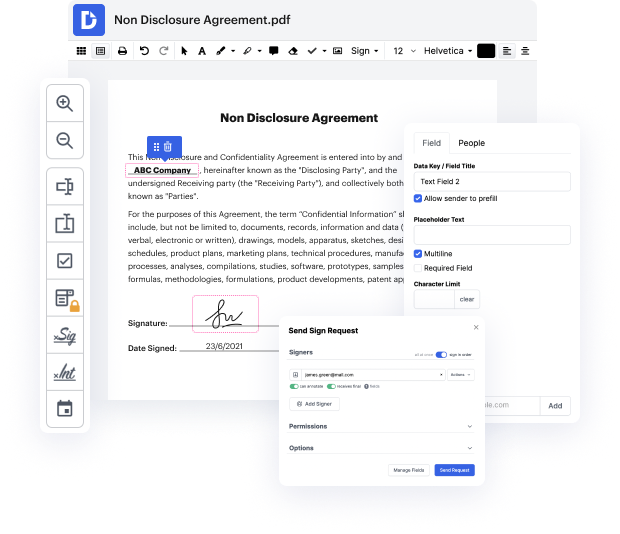
With DocHub, you will work with an editing multitool for just about any situation or file type. Minimize the time you used to spend navigating your old software’s features and learn from our intuitive user interface as you do the job. DocHub is a streamlined online editing platform that handles all of your file processing needs for virtually any file, such as LOG. Open it and go straight to productivity; no prior training or reading guides is required to reap the benefits DocHub brings to document management processing. Start by taking a few moments to register your account now.
See improvements within your document processing just after you open your DocHub account. Save your time on editing with our single solution that will help you be more efficient with any file format with which you have to work.
[Music] hey guys hackersploit here back again with another video and in this video ill be showing you how to clear your tracks on linux operating systems with a variety of tools all right so why is this important now if youre a penetration tester you probably already know why this is important well covering tracks or clearing your tracks is the final stage of penetration of the penetration testing process so just before you start report writing and that video is on its way by the way so do stay tuned for that so clearing your tracks essentially involves clearing or wiping all the activity of an attacker or you being the attacker that is so as to avoid any detection by incident response teams or forensic teams all right so it is vitally important in the penetration testing life cycle and of course if you look at it from a defensive point of view it can really test incident handlers and the blue team in their ability to discover an attacker in in the system whether they do have an int