
Whether you are already used to working with ACL or managing this format the very first time, editing it should not feel like a challenge. Different formats might require specific applications to open and modify them properly. Nevertheless, if you need to swiftly clean caption in ACL as a part of your usual process, it is best to find a document multitool that allows for all types of such operations without extra effort.
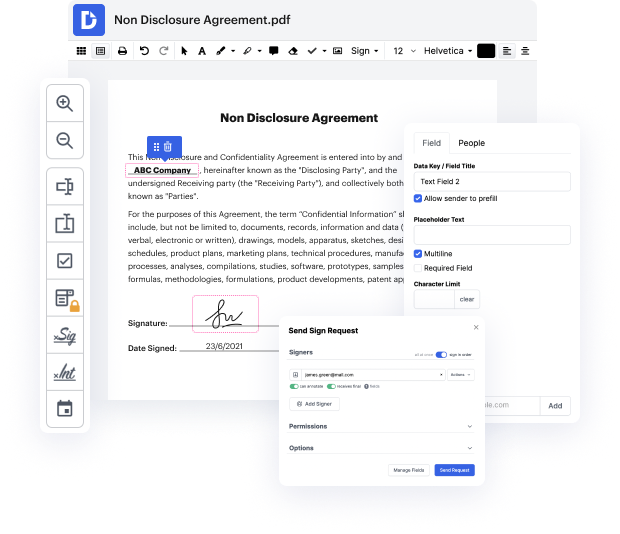
Try DocHub for efficient editing of ACL and other file formats. Our platform offers easy document processing no matter how much or little prior experience you have. With all instruments you need to work in any format, you will not have to jump between editing windows when working with each of your papers. Easily create, edit, annotate and share your documents to save time on minor editing tasks. You will just need to sign up a new DocHub account, and you can start your work right away.
See an improvement in document processing efficiency with DocHub’s straightforward feature set. Edit any file quickly and easily, irrespective of its format. Enjoy all the advantages that come from our platform’s efficiency and convenience.
In this video and the next two videos I will be looking at auditing. Auditing allows you to track Active Directory and file access in your organization. In this video I will look at the concepts behind auditing. How it works and what you need to know to start using it. In the next video I will look at how to configure auditing to track changes in Active Directory. The video after this I will look at how to configure auditing for file and folder access. To start with, I will look at the basic concepts of how auditing works. Lets consider an object in Windows. This could be a file or folder, user or computer account or any other object that exists in Windows. In order to protect the object from unauthorized access you require permissions, these are often referred to as Access control List or ACL. If a user requires access to an object, they require permissions to that object. In order to determine if the user has access they are looked up in an Access Control List called Direct Access