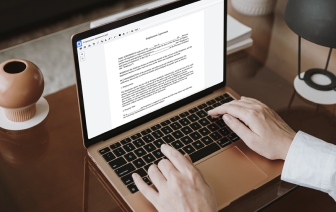
A lot of companies neglect the advantages of complete workflow application. Typically, workflow programs center on a single element of document generation. There are much better alternatives for many sectors that need a versatile approach to their tasks, like Golden Ticket preparation. Yet, it is possible to identify a holistic and multifunctional option that will deal with all your needs and requirements. As an example, DocHub is your number-one option for simplified workflows, document creation, and approval.
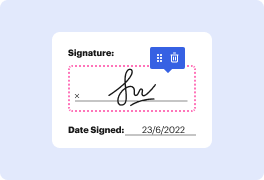
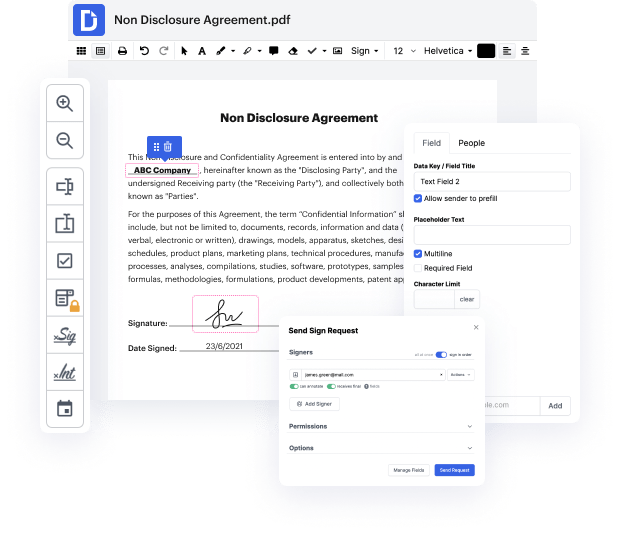
With DocHub, it is possible to generate documents completely from scratch having an extensive set of instruments and features. You are able to easily cancel sign in Golden Ticket, add comments and sticky notes, and track your document’s advancement from start to end. Quickly rotate and reorganize, and blend PDF files and work with any available format. Forget about trying to find third-party solutions to deal with the standard needs of document creation and utilize DocHub.
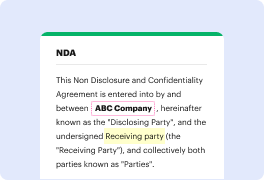
Take complete control of your forms and documents at any time and make reusable Golden Ticket Templates for the most used documents. Take advantage of our Templates to avoid making typical errors with copying and pasting exactly the same details and save your time on this tedious task.
Improve all your document operations with DocHub without breaking a sweat. Find out all opportunities and capabilities for Golden Ticket managing today. Begin your free DocHub profile today with no hidden service fees or commitment.


okay in this video were going to take a look at the Kerberos golden ticket attack now this is not so much a privilege escalation attack where we are going to kind of use it in that way in this video theres more of a persistence attack so its like when youve already got access to some pretty high-level stuff in the domain and as youll see in the demo we do actually have the option of just using the administrator account instead so this is when youve pretty much already compromised the domain this is gonna be a way to keep persistent access to that domain because if they change the administrator account password thats not gonna make any difference for this kind of attack so this machine that were on here is just a separate standalone machine not part of the domain not got any kind of authorization on the domain on the network this machine weve got over here is a domain controller for our target domain this scr m dot local domain is when were trying to attack and now the key pa