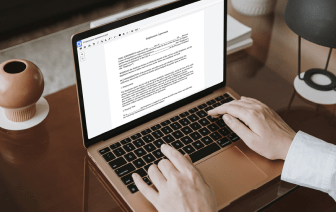

Document generation and approval are a core focus for each company. Whether handling sizeable bulks of documents or a certain contract, you must remain at the top of your productivity. Finding a excellent online platform that tackles your most frequentl document creation and approval obstacles may result in quite a lot of work. Many online platforms provide merely a limited list of modifying and signature features, some of which could be beneficial to handle DBK format. A solution that handles any format and task will be a excellent option when picking application.
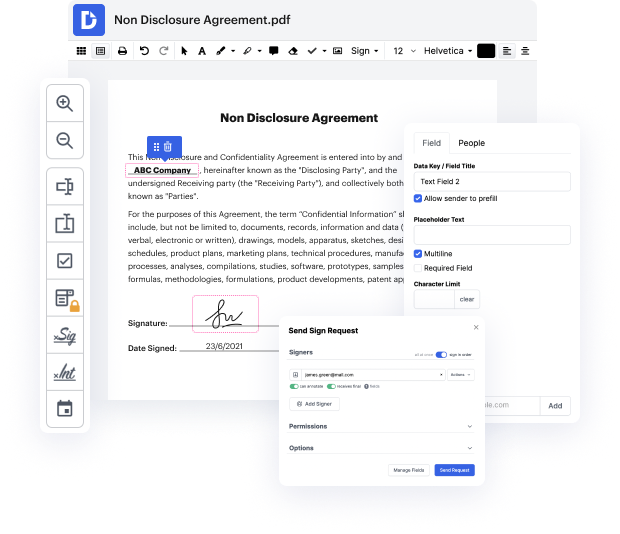
Get file managing and creation to a different level of simplicity and excellence without choosing an difficult interface or pricey subscription plan. DocHub offers you tools and features to deal efficiently with all of file types, including DBK, and execute tasks of any complexity. Change, manage, and make reusable fillable forms without effort. Get full freedom and flexibility to bind token in DBK at any moment and safely store all of your complete files in your profile or one of several possible incorporated cloud storage space platforms.
DocHub offers loss-free editing, eSignaturel collection, and DBK managing on a expert level. You don’t need to go through tiresome tutorials and spend countless hours figuring out the platform. Make top-tier safe file editing a standard process for your day-to-day workflows.
In our example, we have a Client and a Server. The Client wants to access some protected data on our Server, but the Server knows Clients cannot be trusted. The Server only wants to give the data to a trustworthy Client. So our Client sends a request to our Server along with data to verify who it is. In our example, this user data was accepted as valid by the Server. Now instead of saving this user data, the Server instead creates a . This is returned to the Client and its up to the Client to store this data and send it along as required for any requests to the Server. The next time our Client makes a request along a secure route, it does just that. It sends along the job . But our Server knows not to trust the Client because Clients cannot be trusted. So our Server verifies this is who it says its from and that it hasnt been tampered with. If everything checks out like it does in our example, the Server sends back a response with the requested data and everyb