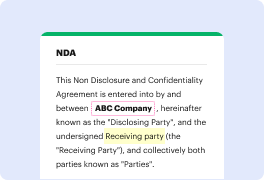
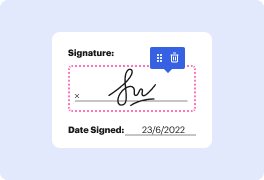
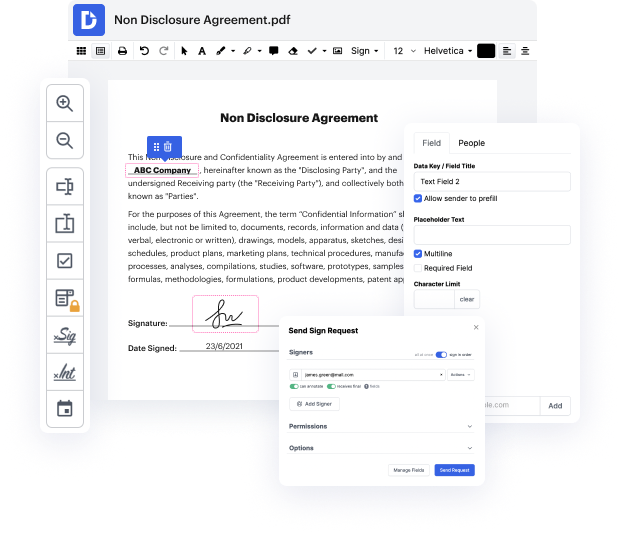
Handling documents like Employment Verification Request might appear challenging, especially if you are working with this type for the first time. Sometimes even a tiny modification might create a major headache when you don’t know how to work with the formatting and avoid making a mess out of the process. When tasked to bind spot in Employment Verification Request, you could always use an image editing software. Others might go with a classical text editor but get stuck when asked to re-format. With DocHub, though, handling a Employment Verification Request is not harder than editing a document in any other format.
Try DocHub for quick and efficient document editing, regardless of the document format you might have on your hands or the kind of document you have to fix. This software solution is online, accessible from any browser with a stable internet access. Modify your Employment Verification Request right when you open it. We have developed the interface so that even users with no prior experience can easily do everything they need. Streamline your forms editing with one streamlined solution for just about any document type.
Working with different types of papers must not feel like rocket science. To optimize your document editing time, you need a swift solution like DocHub. Manage more with all our instruments on hand.
inspector network monitoring software understanding technology blind spots weve identified five IT management blind spots present in every computer network these information voids with a cause of over ninety percent of all network disruptions and threats and have been detected over hundreds of environment Lion spot number one technology improperly configured or not performing correctly this occurs because IT systems cant report on their failures network LAN and traffic analysis can provide independent verification of Technology related issues firewall the firewall is the primary network security appliance firewall rules control what traffic can pass in and out of a local area network inspector software is connected to the network just inside the firewall where it continuously logs analyzes and stores all network traffic flows independently monitoring firewall status along with all internal external communications and usage inspector generates daily and weekly PDF executive reports d
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



