Unusual file formats within your day-to-day papers management and modifying operations can create instant confusion over how to modify them. You may need more than pre-installed computer software for effective and quick document modifying. If you need to bind phone number in jpg or make any other simple change in your document, choose a document editor that has the features for you to deal with ease. To handle all of the formats, including jpg, choosing an editor that actually works well with all types of documents will be your best choice.
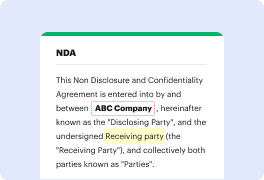
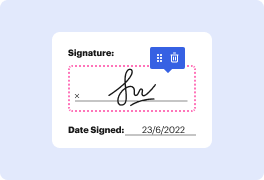
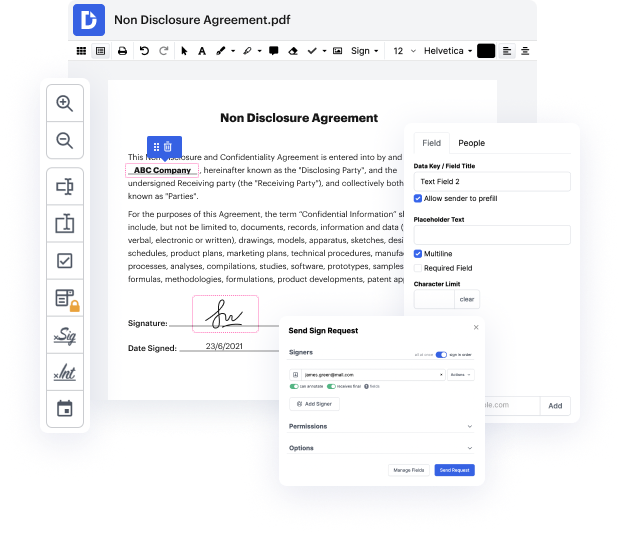
Try DocHub for effective document management, regardless of your document’s format. It has powerful online editing tools that simplify your papers management process. It is easy to create, edit, annotate, and share any papers, as all you need to access these characteristics is an internet connection and an active DocHub account. A single document tool is everything required. Don’t lose time switching between various programs for different documents.
Enjoy the efficiency of working with a tool made specifically to simplify papers processing. See how straightforward it is to revise any document, even when it is the first time you have dealt with its format. Register a free account now and improve your whole working process.
hello everyone welcome to Pber Channel recently I have posted a video how to hide exe payload into image so many people has docHubed to me and comment below the video on hacking Android and shoot it like lot of questions on it so thought to answer all your questions by your video and also sharing my experience in research and testing results if you are watching this video without subscribing I would request to subscribe the channel it will really motivate me to do more interesting content for you guys without further delay lets get into the video question 1 how to hide APK payload into image technically you can create a APK payload and compile or compress with image but when I tester in my lab it is not working just image file open but no reverse connection established at the background also I unable to find any proof of concept from the cyber security professional on this please comment below if you have any proof of concept or relevant article let me res
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



