When your daily tasks scope includes a lot of document editing, you already know that every document format requires its own approach and in some cases particular applications. Handling a seemingly simple docx file can often grind the whole process to a halt, especially if you are trying to edit with insufficient software. To avoid this kind of problems, find an editor that will cover all your requirements regardless of the file format and bind account in docx with zero roadblocks.
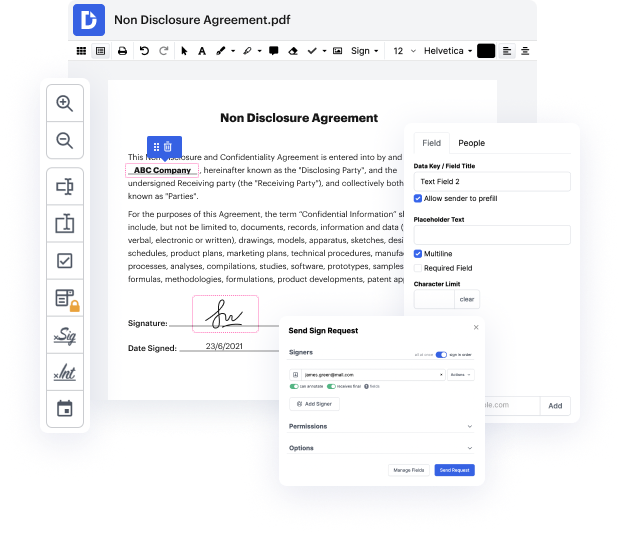
With DocHub, you will work with an editing multitool for just about any occasion or document type. Minimize the time you used to devote to navigating your old software’s features and learn from our intuitive interface design while you do the job. DocHub is a sleek online editing platform that covers all your document processing requirements for any file, including docx. Open it and go straight to efficiency; no previous training or reading instructions is required to enjoy the benefits DocHub brings to papers management processing. Start by taking a few moments to create your account now.
See upgrades in your papers processing immediately after you open your DocHub profile. Save time on editing with our one platform that will help you be more efficient with any document format with which you need to work.
disclaimer the information provided in this video is for general information and educational purposes only students should test cybersecurity techniques in the secured lab setup i do not take any responsibility and i am not liable for any damage or problem caused while implementing the tools and technique so far weve seen how to make our backdoors or trojans look and function like a file that the target person trusts like an image or a pdf or any other file type we did this using our download and run payload and we configured that payload to download two files to download our backdoor and to download an image or the pdf that the person sees then it executes the file that the person sees and it executes our backdoor in the background so the end product was an executable that functions like a normal image or a normal pdf we then had to change the icon of that file to reflect the type of the file that we are trying to spoof and we had to spoof the file extension or the file name again w
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



