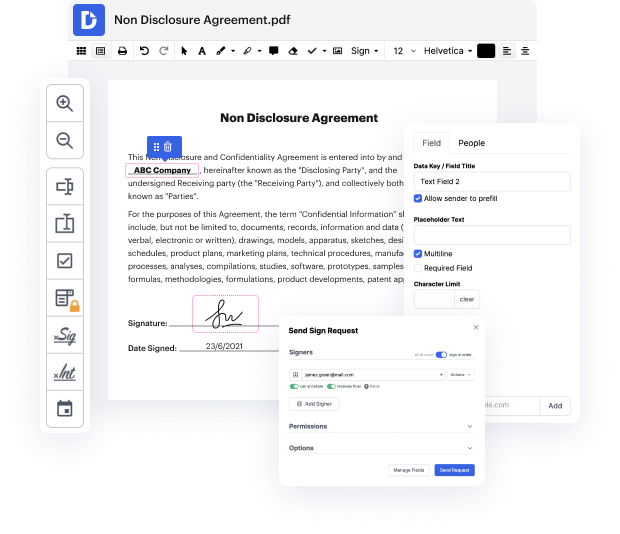
Are you looking for how to Append Tentative Field Work For Free or make other edits to a document without downloading any software? Then, DocHub is what you’re after. It's easy, user-friendly, and secure to use. Even with DocHub’s free plan, you can benefit from its super handy features for editing, annotating, signing, and sharing documents that let you always stay on top of your tasks. In addition, the solution provides smooth integrations with Google services, Dropbox, Box and OneDrive, and others, allowing for more streamlined transfer and export of documents.
Don’t spend hours looking for the right tool to Append Tentative Field Work For Free. DocHub provides everything you need to make this process as smooth as possible. You don’t have to worry about the safety of your data; we comply with regulations in today’s modern world to shield your sensitive data from potential security risks. Sign up for a free account and see how easy it is to work on your documents efficiently. Try it now!
A very common issue that we still constantly encounter is shown in heap level 2 of exploit-exercises.com. This is a classic use-after-free vulnerability. Lets try to understand the code first. We have here a big while loop inside of main. In each round it prints the variable auth, which is a pointer to an object of this auth struct up here. And auth has the attributes name which is a string up to 32 characters and an integer. And the other variable that is printed is a char pointer service, which can point to a string in memory. So both of these are addresses - pointers. Then we read a line from standard input. Maximum 128 bytes, so this is a secure fgets read. No buffer overflow. Afterwards we have a couple of ifs that check if the input line is one of the following commands. Either auth, reset, service or login. Lets execute the program as well and then lets talk about each command. When we first start the program, both the auth and the service pointer are null. Now we wa
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



